The Legal Problem with Relying on Screenshots as Evidence

Text messages have become the default form of communication in nearly every aspect of modern life. They coordinate business deals, document personal relationships, and increasingly, serve as evidence in criminal prosecutions. Walk into any courtroom today and you'll likely see attorneys presenting screenshots of alleged text conversations to prove their case.
But here's the problem: a screenshot is just an image. It doesn't prove when a message was actually sent, who truly authored it, or whether it has been altered. Courts have begun recognizing this fundamental weakness, and defense attorneys who understand how to challenge screenshot evidence can protect their clients from potentially fabricated or misleading digital communications.
This article examines the legal standards for authenticating text message evidence in Texas criminal cases, the strategic challenges defense attorneys face when challenging this evidence, and how forensic analysis can expose screenshots that don't match reality.
Why Screenshots Have Become Common Evidence
The prevalence of text message evidence in criminal cases isn't surprising. According to recent data, Americans send over 6 billion text messages daily. These messages often contain admissions, threats, or contextual information that prosecutors find compelling. When investigators receive a complaint, they often ask for a screenshot or screen recording of any relevant conversations.
Screenshots and screen recordings are convenient. They're quick to capture, easy to share, and visually persuasive. A juror looking at what appears to be a threatening text message displayed in the familiar iMessage or SMS format may find it immediately credible. The visual presentation carries an inherent authority that raw data lacks.
However, this convenience comes at a cost. Screenshots strip away the metadata and technical artifacts that would otherwise help verify authenticity. They present a flat, two-dimensional representation of what is actually complex digital evidence. As one digital forensics expert noted after a case where fabricated screenshots sent an innocent defendant to jail for six months: "Screenshots alone are not enough for court because they're easy to manipulate."
What Texas Courts Require to Admit Screenshot Evidence
Before a screenshot can ever reach a jury, Texas courts require the party offering it to clear a critical legal hurdle: authentication.
The Authentication Standard Under Rule 901
Under Texas Rule of Evidence 901(a), authentication is a condition precedent to admissibility. The proponent must make a threshold showing "sufficient to support a finding that the item is what the proponent claims it is." Whether the proponent has crossed this threshold is a preliminary question of admissibility under Rule 104(a).
The Texas Court of Criminal Appeals has characterized this authentication requirement as a "low bar." In Tienda v. State, 358 S.W.3d 633 (Tex. Crim. App. 2012), the court established that electronic messages can be authenticated through distinctive characteristics, circumstantial evidence, or witness testimony.
But here's the strategic dilemma defense attorneys must confront: while the authentication standard is relatively low, challenging it often requires the defendant to testify. If your client denies sending the messages, they may need to take the stand to explain why the screenshots are inaccurate or fabricated. This exposes them to cross-examination on other matters, a risk many defense attorneys rightly want to avoid.
Wineberg v. State (Tex. App. 2023): A Case Study in Exclusion
The Texas appellate decision in Wineberg v. State illustrates how screenshot evidence can be excluded when the proponent fails to properly authenticate the messages. In that case, the State attempted to introduce screenshots of online chat messages allegedly sent by the defendant.
However, the witness expected to authenticate the messages testified that she did not send them and could not verify their authenticity. The State presented no additional evidence linking the defendant to the messages beyond the screenshots themselves. As a result, the trial court excluded the screenshots for lack of authentication under Texas Rule of Evidence 901, and the court of appeals affirmed that decision.
The significance of Wineberg is not that screenshots are inherently unreliable, but that screenshots alone may be insufficient to authenticate electronic communications when their origin is disputed. When the proponent cannot provide corroborating evidence tying the messages to the alleged sender, courts may exclude the evidence entirely. Proper authentication, through witness testimony, metadata, device analysis, or other supporting evidence, is critical.
The Chain of Cases Establishing Texas Standards
Texas courts have developed a clear body of law on electronic message authentication:
- Butler v. State, 459 S.W.3d 595 (Tex. Crim. App. 2015): The court explained that evidence showing only that a phone number is associated with a particular person may be too tenuous by itself to establish authorship of a text message. The court analogized a phone number to a return address on a letter, it may suggest the sender, but it does not conclusively prove who actually authored the message.
- Tienda v. State, 358 S.W.3d 633 (Tex. Crim. App. 2012): The court observed that "cell phones can be purloined" and thus evidence that a text message emanates from a cell phone number assigned to the purported author, without more, is insufficient to support a finding of authenticity. The court recognized that electronic communications can be sent by someone other than the account holder, noting that devices or accounts can be used by others. However, the court ultimately held that sufficient circumstantial evidence can authenticate electronic communications, including contextual details, photographs, references to events, or other distinctive characteristics linking the messages to the purported author.
- Cain v. State, 621 S.W.3d 75 (Tex. App. Fort Worth 2021, pet. ref'd): The court explained that when a proponent seeks to attribute text messages to a particular person, they must provide additional direct or circumstantial evidence to bridge the logical gap between the phone number and the alleged sender. This may include testimony from a witness with knowledge, contextual references within the messages, or other distinctive characteristics supporting authorship.
Why Screenshots Are Inherently Unreliable
At a technical level, screenshots are one of the weakest forms of digital evidence due to their lack of verifiable data and susceptibility to manipulation.
The Metadata Problem
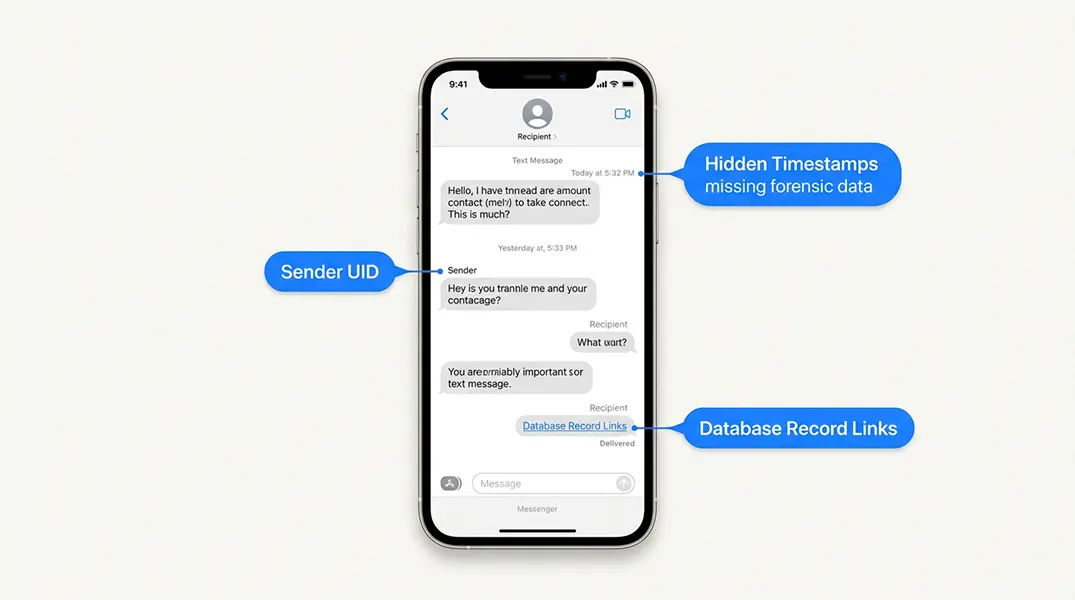
A screenshot captures only what appears on screen at a specific moment. It does not preserve the underlying metadata that forensic examiners rely on to verify authenticity. When we perform a forensic extraction of a mobile device, we access databases like sms.db on iPhones or mmssms.db on Android devices. These databases contain:
- Precise timestamps (often to the millisecond)
- Sender and recipient identifiers
- Message status flags (sent, delivered, read)
- Thread identifiers linking conversations
- Carrier information and routing data
Screenshots capture none of this. The timestamp visible on a screenshot is when the screenshot was taken, not when the message was sent. The contact name displayed can be easily changed in the phone's address book. Without access to the underlying database records, there is no way to verify that what the screenshot shows matches what actually occurred.
How Easy It Is to Fabricate Screenshots
The tools for creating fake screenshots are widely available and surprisingly sophisticated. Anyone with basic technical skills can:
- Use photo editing software like Photoshop to alter names, dates, times, and message content in existing screenshots
- Generate entirely fake conversations using online tools designed specifically for creating realistic-looking text message screenshots
- Manipulate device settings (changing the phone's date and time) to make messages appear to have been sent at different times
- Use browser developer tools to edit the HTML of web-based messaging platforms and capture the modified display
The ease of fabrication is well-documented across online communities. As one user in a legal advice discussion noted: "It's honestly terrifying how easy it is to fake text screenshots. There are literally dozens of free websites where you can create a fake iMessage conversation that looks identical to the real thing. No technical skills needed." This sentiment is echoed repeatedly in forums where users discuss how screenshot evidence should never be taken at face value.
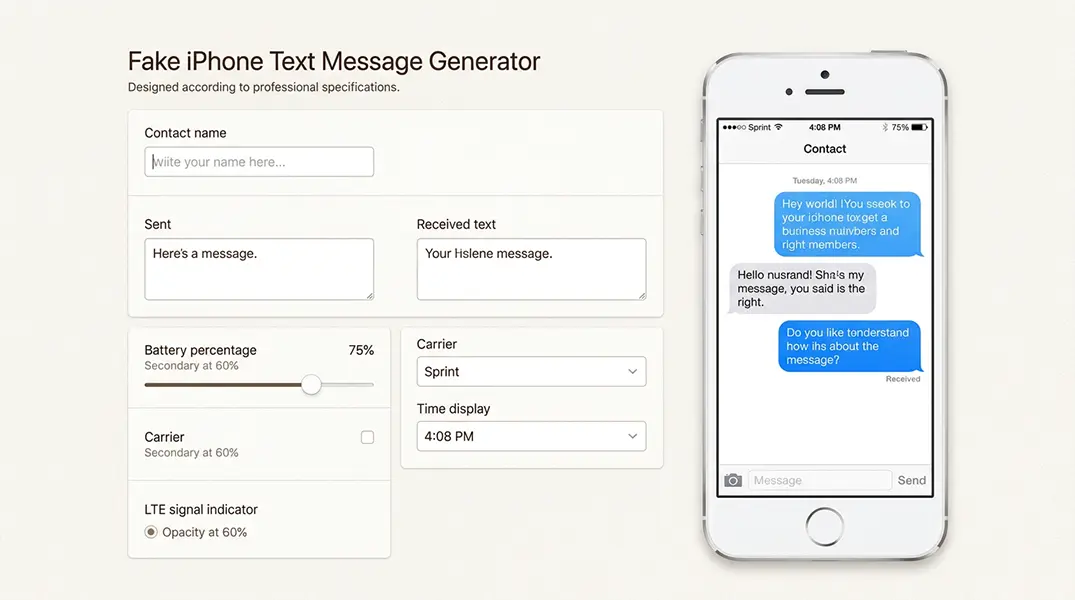
In one case our team worked on, an alleged victim submitted screenshots of threatening messages to law enforcement. The defendant was arrested and spent six months in jail before forensic analysis proved the messages were fabricated. The charges were dropped, but the damage to the defendant's life was substantial and irreversible.
Common Red Flags in Screenshot Evidence
Defense attorneys should train themselves to spot potential indicators of manipulation:
- Visual inconsistencies: Mismatched fonts, unusual timestamp spacing, inconsistent message bubble styling, or variations in battery indicator appearance
- Missing context: Screenshots that show only one side of a conversation, cropped contact information, or sudden gaps in message threads
- Technical anomalies: Screenshot resolution that doesn't match the claimed device, missing or anomalous EXIF metadata, or editing artifacts visible upon close inspection
While these red flags don't prove fabrication, they provide grounds for demanding more rigorous authentication and forensic examination.
How Defense Attorneys Should Challenge Screenshot Evidence
For defense attorneys, effectively challenging screenshot evidence means combining procedural precision with a clear understanding of its technical weaknesses.
Timing and Procedural Strategy
The most effective challenges to screenshot evidence happen outside the jury's presence. Under Rule 104, authentication is a preliminary question for the court. You want to raise these issues in a hearing before trial or during a bench conference, keeping questionable evidence from ever reaching the jury.
If the court overrules your authentication objection and admits the screenshots, preserve the record with running objections for every single message read from the screenshots. This ensures appellate review if the authentication was insufficient. There are numerous cases where a running objection was not lodged, and procedurally, the objection became moot.
Be aware of the strategic trap: challenging authenticity often requires your client to testify that they didn't send the messages. Prosecutors know this. They may introduce screenshot evidence, knowing that the defense's only effective challenge requires exposing the defendant to cross-examination. Consider whether forensic analysis can provide an alternative path to challenge the evidence without requiring your client to take the stand.
Objection Framework
When screenshots are offered, consider these objections:
- Lack of foundation under Rule 901(a): The proponent has not shown sufficient evidence to support a finding that these screenshots are what they claim to be
- Best Evidence Rule (Rule 1002): If the original device or database is available, the screenshot is a duplicate that should be excluded in favor of the original
- Hearsay: The statements contained in the messages may be inadmissible hearsay, and authentication is a separate prerequisite that must also be satisfied
- Request for production: Demand access to the original device for forensic examination to verify the screenshots against the source data
Discovery Tactics
Don't accept screenshots at face value. Use discovery to demand:
- Forensic extraction of the source device by a neutral examiner
- Production of message database files (sms.db, mmssms.db, or equivalent)
- Carrier records for the relevant time period to verify message transmission
- Complete chain of custody documentation showing how the screenshots were captured, stored, and transferred
If the prosecution cannot or will not produce the underlying data, argue that the screenshots lack sufficient foundation for admission.
How Digital Forensics Can Prove Screenshots Are Inaccurate
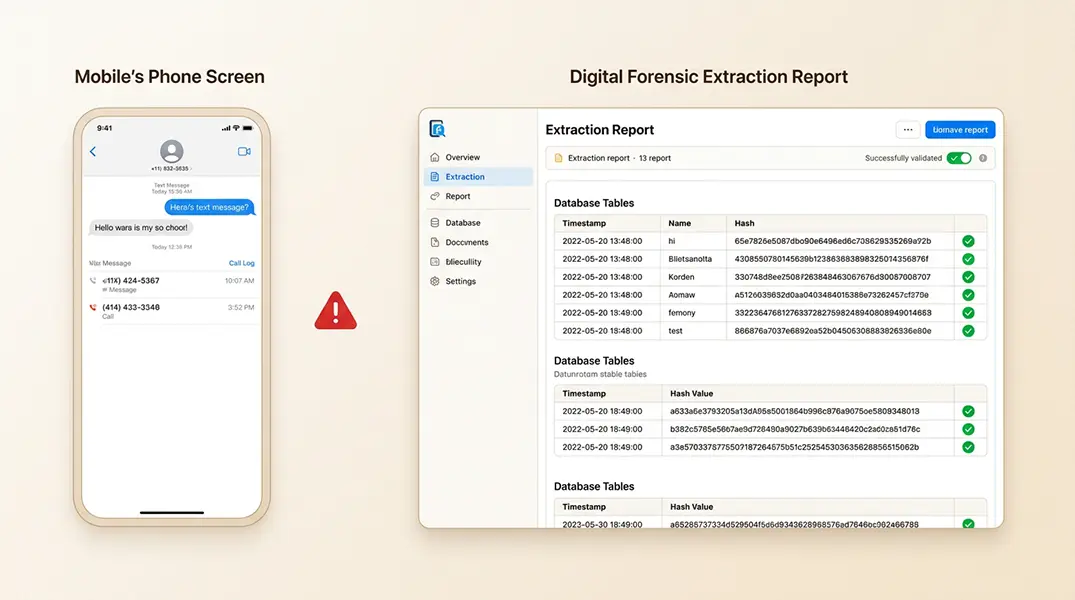
Unlike screenshots, digital forensic analysis examines the underlying data itself, allowing experts to confirm or refute the accuracy of alleged message evidence.
Full File System Extraction
When we conduct a forensic examination of a mobile device, we use specialized tools like Cellebrite, Magnet AXIOM, or Oxygen Forensic Detective to create a complete digital copy of the device's contents. This extraction captures:
- All message databases with their original metadata
- Deleted messages that may still exist in unallocated space
- Application data showing messaging app usage
- System logs that can corroborate or contradict screenshot timestamps
The extraction process generates hash values (digital fingerprints) that prove the data hasn't been altered. If the extracted data doesn't match the screenshots, you have objective proof of fabrication or error.
Timeline and Metadata Analysis
Forensic examiners can compare the timestamps shown in screenshots against:
- The actual message timestamps in device databases
- Carrier records showing when messages were transmitted
- Device activity logs showing when the phone was in use
- Location data that may contradict claimed message origins
Discrepancies between screenshot timestamps and forensic data provide powerful evidence that the screenshots are unreliable.
When Forensic Analysis Excludes Screenshots
In one recent case, our team was asked to examine screenshots allegedly showing incriminating messages sent by a defendant. The forensic extraction of the defendant's phone showed no record of these messages in the SMS database. The timestamps on the screenshots corresponded to times when the phone was not in use, according to system logs. Additionally, the actual messages that did exist had times that were not consistent with what the phone had recorded, and we were able to disprove the messages and show that the screenshot was not valid. The prosecution's key evidence crumbled under technical scrutiny.
Our cell phone forensics services can provide the technical analysis needed to challenge questionable screenshot evidence and present findings in court through expert testimony.
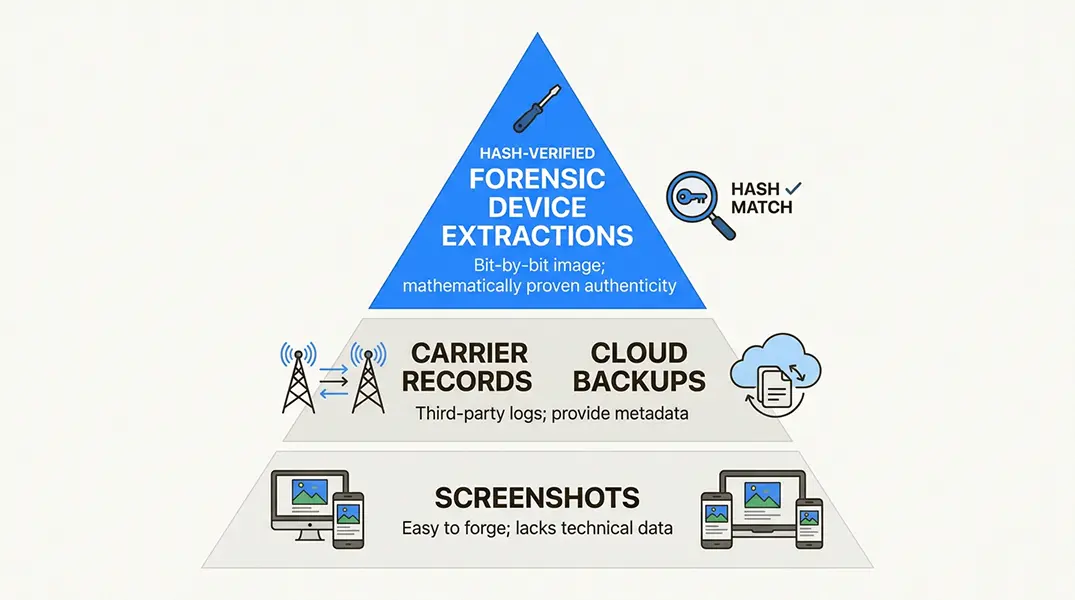
Stronger Forms of Text Message Evidence
While screenshots are weak evidence, properly authenticated digital communications can be powerful. The gold standard includes:
- Forensic device extractions: Complete, hash-verified copies of device data with all metadata intact
- Carrier records: Official records from telecommunications providers showing message transmission data (where recorded)
- Cloud backup analysis: iCloud, Google, or other backup data that preserves message content and metadata
- Messaging platform records: Server-side data from platforms like WhatsApp or Signal when available or through legal process
These sources provide the foundation and metadata that screenshots lack, making them far more resistant to authentication challenges.
Protect Your Client From Unreliable Screenshot Evidence
Screenshots may appear persuasive to jurors, but they lack the forensic foundation required for reliable evidence. Texas courts have established clear standards for authentication, and defense attorneys who understand these standards can effectively challenge screenshot evidence before it ever reaches the jury.
The key takeaways for defense practice:
- Challenge authentication early and outside the jury's presence
- Preserve the record with running objections when screenshots are admitted
- Use discovery to demand underlying data and forensic examination
- Consider whether forensic analysis can challenge evidence without requiring defendant testimony
- Remember that every screenshot should be challenged to preserve the record
At Black Dog Forensics, we specialize in the forensic analysis of digital evidence for criminal defense. Our expert testimony services have helped attorneys challenge unreliable screenshot evidence and protect their clients from wrongful convictions based on fabricated or misattributed digital communications.
If you're facing screenshot evidence in a criminal case, contact us to discuss how forensic analysis can strengthen your defense strategy. We follow rigorous protocols for evidence preservation and chain of custody, ensuring our findings meet the standards for admissibility in Texas courts.




 346-200-6097
346-200-6097




