What Makes a Forensic Image Reliable in Court

When attorneys and investigators first hear the term "forensic image," many might picture crime-scene photographs or digitally enhanced photos for court presentation. In digital forensics, however, the term carries a very different meaning. A forensic image is not a photograph at all. It is a complete, bit-for-bit copy of the digital storage media, capturing every sector, every byte, and every hidden area of a hard drive, smartphone, or other storage device.
Understanding what a forensic image is and why it matters can make the difference between evidence that holds up in court and evidence that gets dismissed on technical grounds. This guide explains the technical foundations of forensic imaging, the standards that govern it, and why it remains the cornerstone of every defensible digital investigation.
What Is a Forensic Image? The Formal Definition
According to standards established by the International Association of Computer Investigative Specialists (IACIS) and the Scientific Working Group on Digital Evidence (SWGDE), a forensic image refers to capturing all data from a piece of source media in a forensically sound manner, ensuring the original data on the source media remains unaltered.
Consider what this means in practice.
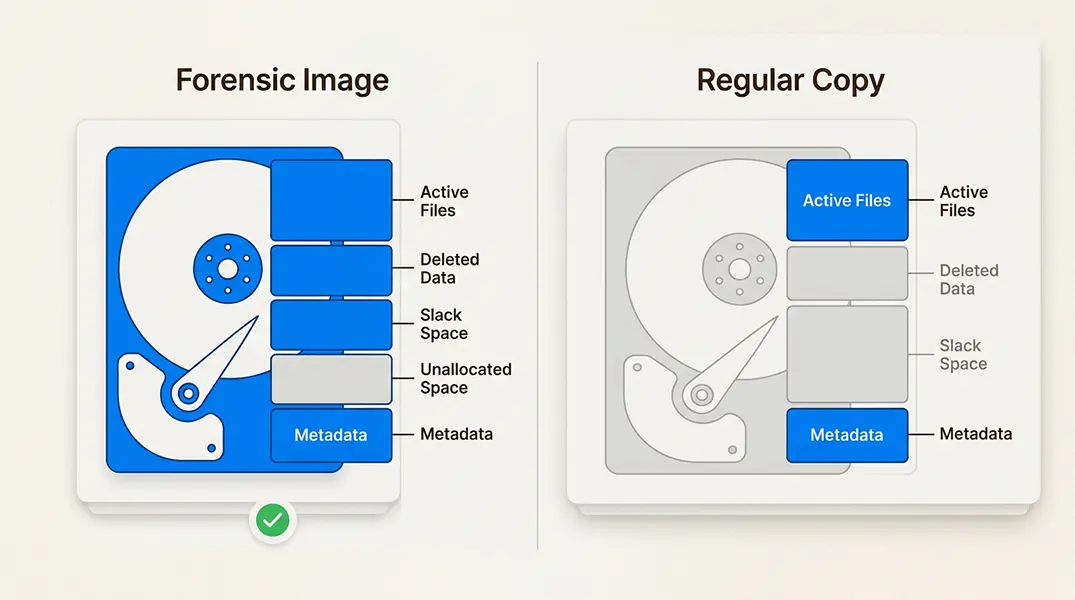
A forensic image is a bit-for-bit, sector-by-sector copy of a storage device. Unlike the file copies you might make by dragging documents to a backup drive, a forensic image captures everything. The operating system only shows you allocated files, the documents and folders currently in use. A forensic image goes deeper, capturing deleted files, empty space that still contains data fragments, hidden partitions, and areas of the disk that commercial operating systems cannot even see.
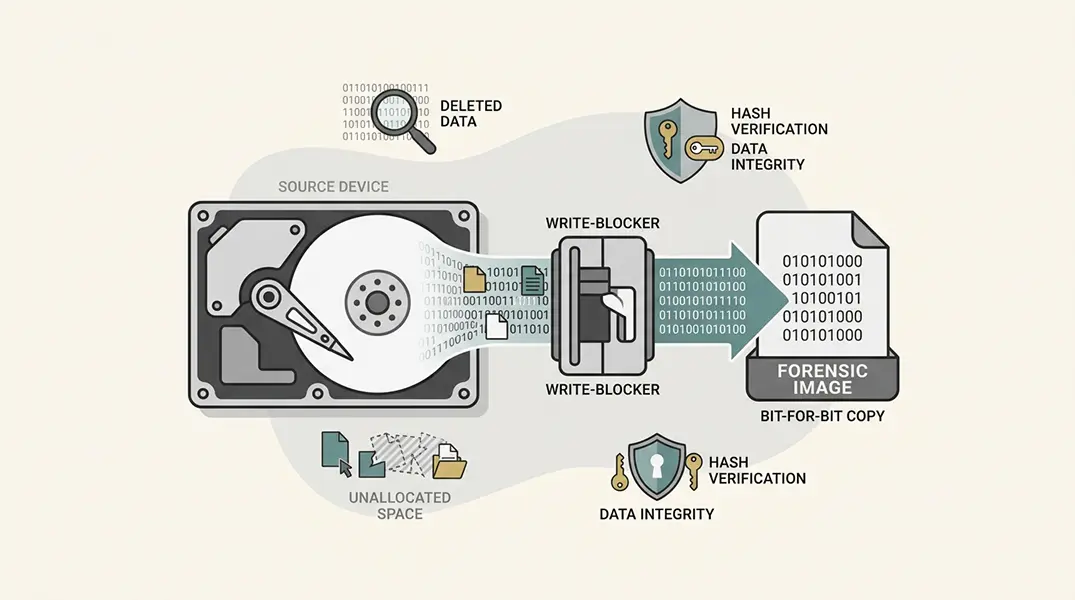
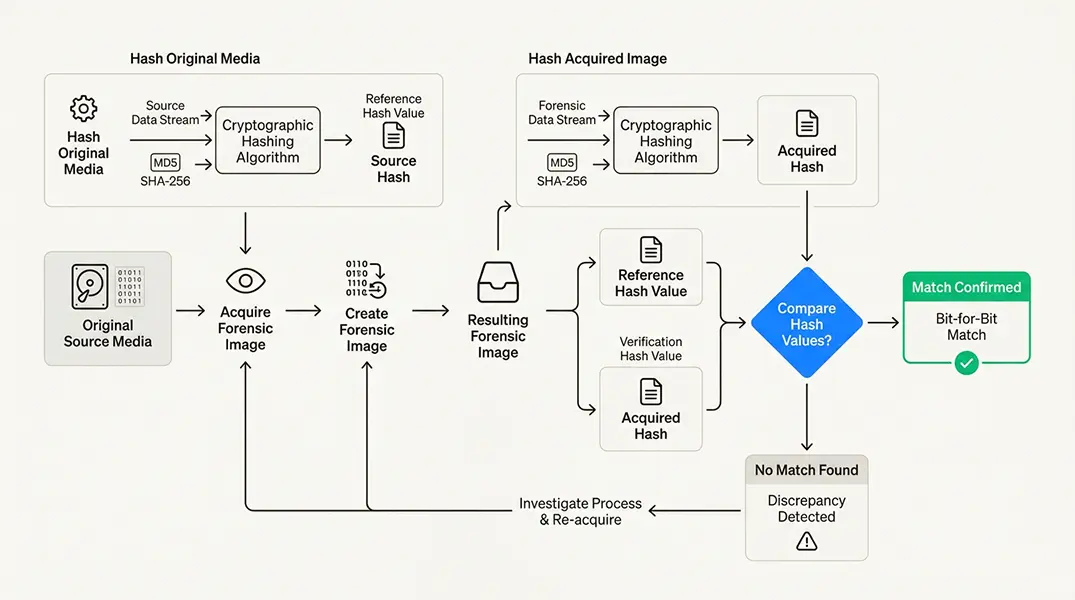
The "forensically sound manner" requirement is equally important. This means the imaging process must not alter the original evidence in any way. Investigators use hardware write-blockers to prevent any write commands from reaching the source device. They document every step. They calculate cryptographic hash values to prove the copy is identical to the original. Any deviation from these standards potentially risks contaminating the evidence and destroying its value in court.
The difference between regular copying and forensic imaging is substantial. When you copy files through your operating system, you capture only active files that the OS knows about. You miss deleted data. You miss fragments of files in slack space. You miss hidden partitions and system areas. For a criminal investigation or civil litigation, that missing data might contain the critical evidence that proves your case. Not to mention merely copying files through an OS can alter that data directly.
What Data Is Captured in a Forensic Image?
A forensic image captures areas of a disk that normal copying simply cannot reach. Understanding these areas helps explain why forensic imaging is non-negotiable for serious investigations.
Areas of the Drive Captured
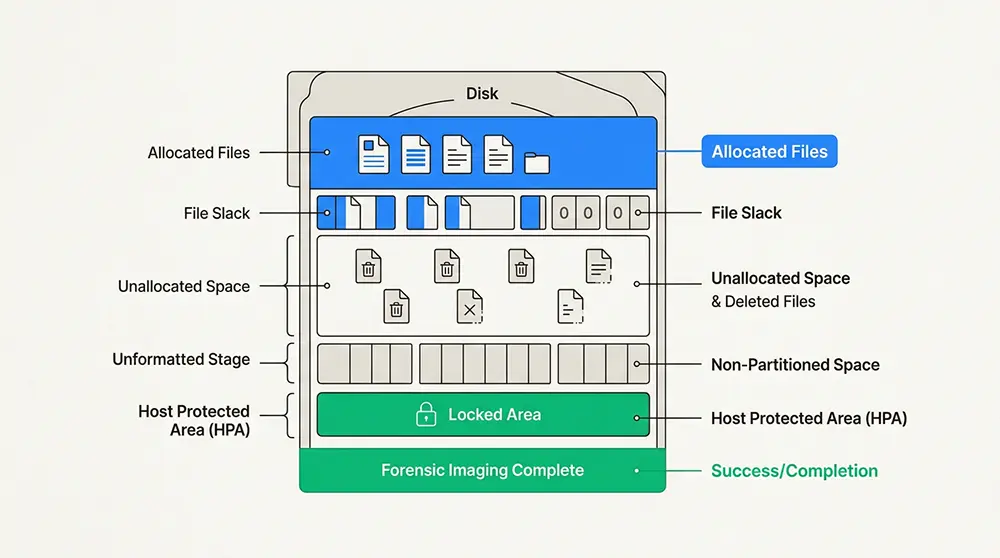
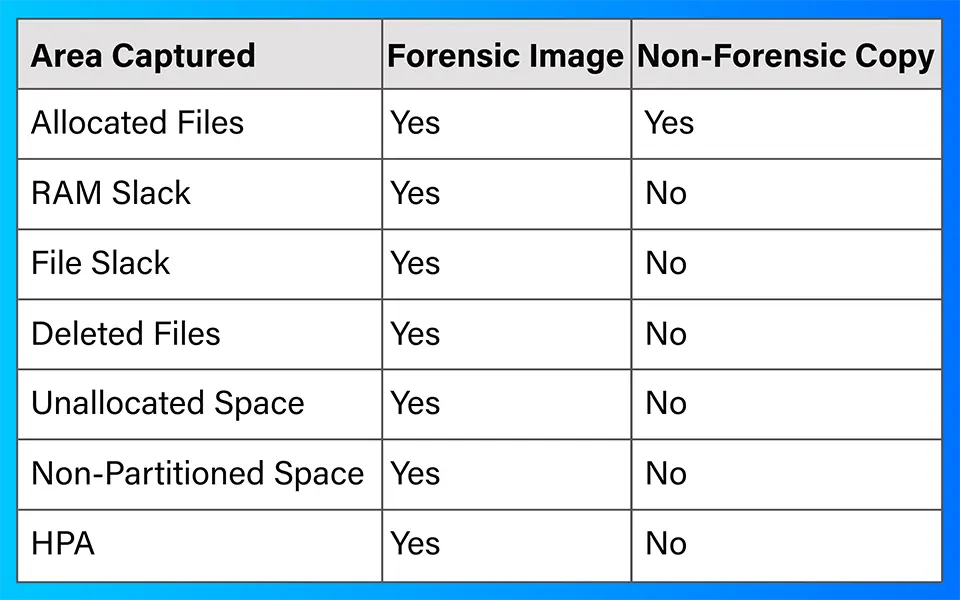
Allocated files are the files and folders currently visible to the operating system. These include documents, images, applications, and system files. Both forensic imaging and regular copying capture these files, though forensic imaging preserves additional metadata that regular copying often strips away.
File slack represents the unused space within the last cluster allocated to a file. When a file does not fill an entire cluster, the remaining space in that cluster contains whatever data was previously stored there. This "slack space" can contain fragments of old documents, emails, or other evidence that users thought they deleted.
RAM slack is a specific type of slack space with historical significance. Older operating systems would pad the remainder of a sector with whatever happened to be in memory at the time. This RAM slack could contain cryptographic keys, passwords, or other sensitive data that was never intentionally written to disk.
Deleted files in unallocated space present some of the most valuable evidence in digital forensics. When a user deletes a file, the operating system typically just marks the space as available for reuse. The actual data, depending on the hardware, typically remains on the disk until overwritten. Forensic imaging captures this unallocated space, allowing investigators to recover deleted documents, photos, chats, and other files that would otherwise have gone forever.
Non-partitioned space refers to areas of the disk that are not assigned to any recognized partition. Sophisticated users might hide data in these areas to evade detection. A forensic image captures everything, including these hidden corners of the storage device.
The Host Protected Area (HPA) is a reserved area on hard drives that is normally invisible to the operating system. Originally designed for system recovery and diagnostic tools, the HPA can also be used to hide data. Many forensic imaging tools can access and capture the HPA, ensuring no evidence escapes detection.
Comparison Table: Forensic Image vs Non-Forensic Copy
Why These Areas Matter for Investigations
Deleted file recovery often produces the most compelling evidence in digital investigations. A user might delete incriminating emails, financial records, or communications thinking they have covered their tracks. Forensic imaging preserves these deleted data in unallocated space, allowing investigators to recover these files and establish timelines of activity.
Evidence of data destruction attempts can be just as valuable as the data itself. When a user runs wiping software or attempts to overwrite incriminating files, these actions leave traces. Forensic imaging captures the before-and-after state of the disk, potentially proving that someone tried to destroy evidence.
Hidden data and partitions sometimes contain the most sensitive material. Whether it is corporate trade secrets, evidence of fraud, or communications related to criminal activity, sophisticated actors know how to hide data from casual inspection. Forensic imaging ensures these hiding places are examined.
Timeline reconstruction depends on capturing every timestamp and metadata field from the original media. File creation times, modification times, access times, and other metadata help investigators establish when events occurred and who was responsible. Regular copying often strips or alters this critical metadata.
Forensic Copy vs Forensic Evidence Files
Digital forensics recognizes two primary forms of forensic imaging, each with specific use cases and characteristics.
Forensic Copy (Direct Bit-for-Bit Copy)
A forensic copy is a direct bit-for-bit copy of original media written to target media of equal or larger capacity. When creating a forensic copy, any unused space on the target media is overwritten with zeros (0x00). The result is an exact duplicate that can be used exactly like the original drive.
This method is typically used when investigators need a working drive that can be mounted, booted, or analyzed just like the original. Some analysis techniques require direct access to the physical drive structure, making forensic copies necessary.
Forensic Evidence Files (Container Formats)
Forensic evidence files are container formats that store the bit-for-bit data from the original media along with additional metadata. The most common formats include:
E01 (EnCase Evidence File) is a common industry standard format developed by Guidance Software (now OpenText). NIST's Computer Forensics Tool Testing (CFTT) Program validates forensic tools that create and analyze E01 files to ensure they meet established standards. E01 files contain not only the forensic image data but also other information in the file header. The format includes built-in CRC verification and supports compression and encryption.
DD/RAW format represents a raw bit-for-bit copy without the container structure of E01. DD files contain only the data from the source media with no embedded metadata. While simpler, DD files require external hash files and documentation to maintain the chain of custody.
Why Investigators Avoid Working on Original Evidence
Digital forensic examiners should ideally avoid conducting examinations directly on original evidence media, a principle reinforced by IACIS training standards and NIST guidelines. This principle exists for several reasons.
Digital evidence is fragile. Simply mounting a drive can alter timestamps and metadata. Opening a file can change its access time. Even read-only access can trigger background processes that modify the disk. By working exclusively on forensic images or copies, investigators ensure the original evidence remains pristine.
The reproducibility principle requires that any forensic analysis be repeatable by another qualified examiner. If the first examiner works on the original and accidentally alters something, no one can reproduce the original state. Working from forensic images preserves the original while allowing multiple examiners to analyze copies independently.
Exceptions do exist. Time-sensitive investigations might require immediate analysis of a running system to capture volatile memory data. Technical limitations might prevent imaging of certain embedded systems. Device constraints might make imaging impractical. In these cases, examiners document every action and explain why deviation from standard practice was necessary.
DD vs E01: Understanding Forensic Image Formats
The choice between DD and E01 formats has practical implications for investigators.
DD (Raw) Format
DD format creates a bit-for-bit uncompressed copy of the source media with no compression applied. The resulting file is exactly the size of the original device. For large drives, DD files may be split into multiple segments with extensions like .001, .002, and so on.
The primary advantage of DD format is universal compatibility. Virtually every forensic tool can read DD images. The simple structure means DD files can be mounted as drives in most operating systems without special software. The lack of compression also means faster imaging speeds.
The disadvantages are equally significant. DD files offer no built-in integrity verification. If a DD file becomes corrupted, you might not know until analysis fails. The format stores no case metadata, requiring external documentation for chain of custody. The lack of compression means DD files consume maximum storage space.
E01 (Expert Witness Format)
E01 format was developed specifically for forensic use and has become an industry standard. The format stores case information in the file header, including acquisition notes, examiner data, timestamps, and system details. E01 files include a Cyclical Redundancy Check (CRC) verification with a 32-bit value calculated to ensure data has not changed within the block during the copying process. At the end of the evidence file, an MD5 is calculated for all the data blocks. The header and individual CRCs are not included in the MD5 calculation. The MD5 value is then including in the forensic evidence file, shown below.
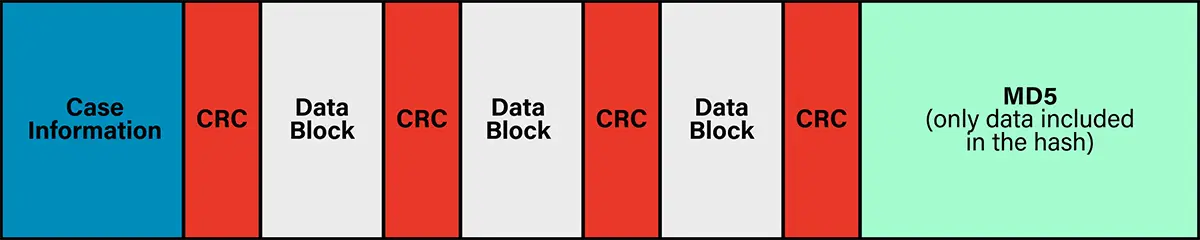
When the data is later read or verified, the same CRC calculation is performed again. If the newly calculated CRC value matches the original CRC value, the data block is assumed to be intact. If the values differ, it indicates that the data was altered or corrupted during copying, storage, or transmission.
The main disadvantage is that E01 is technically a proprietary format, though it is widely supported across forensic tools. The compression and metadata features add complexity that some simple tools cannot handle.
Choosing the Right Format
Use DD format when you need maximum compatibility, fastest imaging speeds, or when working with tools that do not support E01. DD is also appropriate when storage space is not a concern and you maintain rigorous external documentation.
Use E01 (or other more advanced formats) for legal proceedings where built-in integrity verification and metadata are valuable. E01 is preferred when storage space is limited and when you want self-documenting evidence files. Most professional forensic laboratories standardize on E01 (or similar forensic format) for these reasons.
Ensuring Integrity: CRC and Hash Verification
The integrity of forensic images is verified through multiple mechanisms, each serving a different purpose in the evidence preservation process.
CRC (Cyclical Redundancy Check)
CRC plays a specific role in E01 files. Data blocks within E01 files are verified using CRC values calculated during imaging. By default, E01 files use 64 sectors per block, as documented in forensic imaging standards. The CRC value for each block confirms that the block was copied without error during acquisition.
CRC verification helps ensure the integrity of the forensic image during the acquisition process itself. If a sector fails to copy correctly due to hardware issues or transmission errors, the CRC check will detect the problem immediately. This allows investigators to address issues before the imaging process is complete.
It is important to note that CRC headers are not included in the MD5 hash calculation. The hash covers only the actual data blocks, not the CRC metadata.
MD5 and SHA Hash Verification
At the end of the imaging process, forensic tools calculate cryptographic hash values of the original media and the forensic image. The most common algorithms are MD5 and SHA-256.
MD5 produces a 128-bit hash value represented as a 32-character hexadecimal string. While MD5 has known collision vulnerabilities and is being phased out for some security applications, it remains widely used in digital forensics for legacy compatibility and because the collision attacks require specific conditions not present in typical forensic scenarios.
SHA-256 produces a 256-bit hash value represented as a 64-character hexadecimal string. NIST and most forensic standards organizations, including SWGDE, now recommend SHA-256 for new implementations due to its stronger collision resistance.
The hash comparison process is straightforward. The examiner calculates the hash of the original media before imaging. After creating the forensic image, the examiner calculates the hash of the image file. If the hashes match, the image is proven to be a bit-for-bit identical copy of the original. Any discrepancy indicates that something has changed, either during imaging or afterward.
Chain of Custody Documentation
Hash verification is only one component of maintaining evidence integrity. Chain of custody documentation tracks every person who handled the evidence, every action taken, and every location where the evidence was stored. For digital evidence, this includes:
- Who performed the imaging
- When the imaging occurred
- What tools and hardware were used
- The calculated hash values
- Where the evidence was stored
- Who accessed the evidence and when
An unbroken chain of custody is essential for court admissibility. Defense attorneys routinely challenge digital evidence on chain of custody grounds. Without proper documentation, even a perfect forensic image can be excluded or suppressed from evidence.
Terminology Clarification in Digital Forensics
Precision in terminology matters in legal proceedings. The digital forensics field has historically used various terms to describe forensic images, but not all of these terms are accurate or appropriate for court testimony.
Commonly Misused Terms
"Mirror image" suggests that data is reversed like a mirror reflection. This is not what happens in forensic imaging. The term has persisted in some legal contexts but should be avoided in technical testimony as jurors might become confused.
"Exact copy" might seem precise, but it can imply that the target drive is identical in all respects to the source, including physical characteristics like sector counts and drive geometry. Forensic images capture logical data, not physical drive properties.
"Disk cloning" and "disk duplication" are terms from the IT world that describe making functional copies of drives for deployment or backup. These processes often do not capture unallocated space, deleted files, or hidden areas. Using these terms to describe forensic imaging is imprecise and potentially misleading.
"Bit-stream image" is closer to the correct concept but still incomplete. When forensic evidence files include metadata, case information, and verification data, they are more than just a stream of bits from the source media.
Preferred Terminology
The most accurate and legally defensible terms are:
- Forensic Image: The broad term for any forensically sound copy of digital media
- Forensic Copy: A direct bit-for-bit copy written to target media
- Forensic Evidence Files: Container formats like E01 that include metadata and verification data
Why Precision Matters in Legal Context
Court testimony requires clarity. When an expert witness uses imprecise terminology, defense attorneys can exploit the ambiguity to challenge the evidence. An expert who refers to "cloning" might have to explain why their process differs from standard IT cloning procedures.
Expert witness credibility depends on precise, accurate testimony. Using established forensic terminology demonstrates professionalism and adherence to industry standards. It reduces the risk of successful challenges and helps judges and juries understand the evidence.
Why Forensic Imaging Is the Foundation of Digital Investigations
Every defensible digital forensic investigation begins with proper forensic imaging. Without it, the entire investigation lacks a reliable foundation.
Forensic imaging provides the evidence integrity guarantee that courts require. By creating an unaltered copy of the original media and verifying its integrity through cryptographic hashes, investigators can demonstrate that their analysis is based on authentic evidence. This foundation is essential for criminal prosecutions, civil litigation, corporate investigations, and regulatory matters.
Legal admissibility requirements are increasingly strict. Courts have excluded digital evidence because investigators failed to use write-blockers, did not document their procedures, or could not prove that their forensic image was identical to the original. Following established forensic imaging standards prevents these serious failures.
Reliable analysis requires reliable data. When investigators work on verified forensic images rather than original media, they can explore the evidence thoroughly without risk of contamination. They can test hypotheses, run multiple tools, and even make mistakes, all while preserving the original evidence untouched.
The applications span virtually every type of legal matter. In litigation, forensic images preserve evidence of trade secret theft, employment misconduct, or contract breaches. In criminal investigations, they capture communications, location data, and digital artifacts that prove or disprove allegations. In corporate settings, they document policy violations, data exfiltration, and insider threats.
Knowing when to engage professional forensic services is critical. While some IT departments have basic imaging capabilities, complex investigations require specialized expertise. Proper forensic imaging demands knowledge of write-blocking hardware, imaging software, hash verification, chain of custody procedures, and legal standards.
When to Contact a Professional Forensic Examiner
Certain situations demand immediate professional intervention:
- Active litigation or anticipated legal proceedings where evidence admissibility will be challenged
- Criminal investigations requiring testimony from a certified forensic examiner
- Corporate data breaches involving trade secrets, intellectual property, or regulated data
- Employee misconduct cases that may result in termination or legal action
- Insurance fraud investigations require a documented chain of custody
- Any situation where original evidence cannot be reacquired if mishandled
At Black Dog Forensics, we maintain certifications including the Certified Forensic Computer Examiner (CFCE) credential from IACIS. Our examiners follow established protocols from NIST, SWGDE, and IACIS to ensure every forensic image meets court admissibility standards. We bring decades of combined experience to every imaging project, ensuring that evidence is captured correctly the first time and will withstand scrutiny in any legal forum.
If you are facing a situation that requires forensic imaging, contact Black Dog Forensics for a consultation. The integrity of your evidence depends on the actions taken in the first hours of an investigation.




 346-200-6097
346-200-6097




