Why companies wait too long to investigate employee data theft

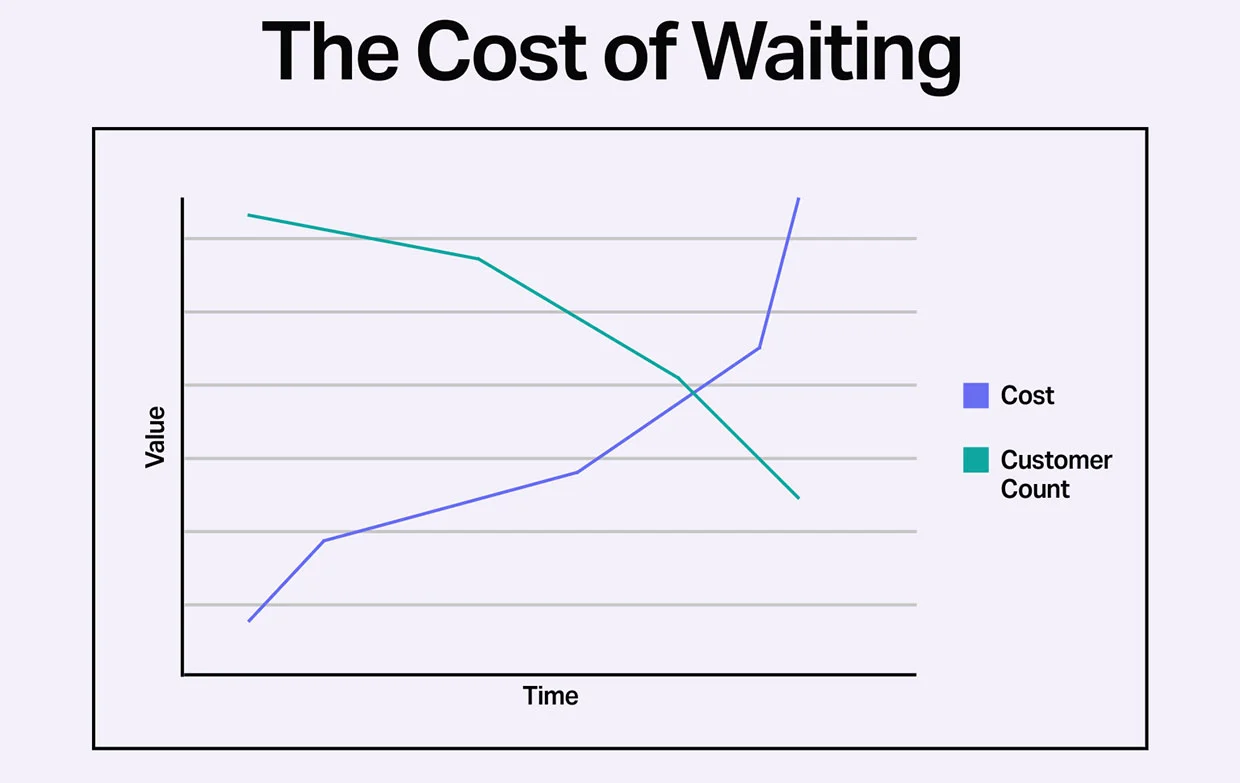
Business owners face a critical choice that could determine the future of their company. It starts with a suspicion, a gut feeling that something isn't right. The decision they make in that moment, whether to conduct an employee data theft investigation or wait and see, often determines whether they spend $5,000 now or $100,000 later.
The Call That Starts It All
For Black Dog Forensics, it usually begins with a phone call that sounds something like this: "I think my employee might have taken some files before leaving. We just want to know if anything was copied."
The voice on the other end belongs to a business owner, CEO, or HR director. They're uneasy but not certain. A trusted employee recently resigned or was terminated, and something about the departure felt off. Maybe there was unusual activity in the final weeks. Maybe the employee was suddenly working odd hours. Or maybe it's just a gut feeling that something isn't right.
We receive calls like this every day. They're so common that we can almost predict how the conversation will unfold. The owner wants to "just check" whether anything happened. They hope we can provide quick clarity and verbal reassurance without escalating the situation unnecessarily.
During the initial consultation, we ask a series of standard questions:
- When did the employee leave?
- Do you still have their company computer and phone?
- Did they have access to customer lists, pricing models, sensitive or proprietary information?
- Was there any unusual behavior in the weeks before departure?
- Did they go work for a competitor?
Based on the answers, we typically recommend an employee data theft or employee departure investigation. This isn't a fishing expedition. It's a targeted forensic analysis that examines specific digital artifacts to determine whether data exfiltration occurred.
A typical forensic analysis costs between $3,500 and $5,000. For that investment, you receive:
- Forensic imaging of the employee's computer, creating a bit-by-bit copy that preserves evidence integrity
- Artifact review examining USB device logs, file transfer records, and system timestamps
- Cloud activity analysis identifying uploads to personal Dropbox, Google Drive, or OneDrive accounts
- Email forwarding detection revealing whether work emails were sent to personal accounts
- Timeline reconstruction showing exactly what happened in the days and weeks before departure
The goal is straightforward: provide clarity. Either the investigation finds evidence of data theft (giving you options for legal action), or it confirms that there is no evidence that inappropriate activity occurred (giving you peace of mind).
The Decision Point
This is where the story often takes a wrong turn.
When we present the $3,500 to $5,000 estimate, we hear variations of the same response: "That seems like a lot of money just to check." Or: "Let's wait and see if anything actually happens." Or: "I don't want to escalate things unnecessarily."
The psychology behind this hesitation is understandable. Business owners work hard to keep cash flow stable, and they want to believe their employees are trustworthy. They assume that if someone resigned professionally, they'll move on professionally. They hope the issue will resolve itself without confrontation. They do not want to seem paranoid.
No one wants to be the employer who investigates every departing employee. What if nothing is found? Will it damage relationships with remaining staff? Will it create a culture of distrust?
During these conversations, we try to warn clients about what happens next. Evidence of digital activity doesn't last forever. In fact, it degrades quickly. Here's what typically occurs in the months following an employee's departure:
- Devices get reassigned. That laptop sitting in the corner gets wiped and handed to a new hire. The forensic artifacts that could have revealed USB connections or file transfers are overwritten.
- Cloud credentials change. When the employee's accounts are deactivated, access logs that showed file uploads may become unavailable.
- Email retention expires. Many companies have 30, 60, or 90-day retention policies. After that period, the record of emails forwarded to personal accounts is gone.
- System logs are purged. Server logs that track network activity have limited storage. Older entries are automatically deleted to make room for new data.
We explain that if data theft occurred, the best strategy is early intervention. A forensic investigation that confirms theft allows your attorney to send a demand letter or cease-and-desist notice immediately. In some cases, you can seek an injunction to prevent the employee from using or sharing your proprietary information while the case proceeds.
The goal isn't just to prove what happened. It's to stop the damage before it spreads.
Six Months Later
When we don't hear back after that initial consultation, we know there's a good chance we'll hear from the same business owner again. It usually takes about six months.
The second call has a completely different tone. The unease has been replaced by urgency. The uncertainty has been replaced by certainty that something is very wrong.
This time, the owner says things like:
- "Our clients are being contacted by a competitor we didn't even know existed."
- "The former employee launched a competing business using our exact pricing model."
- "They have our internal strategy documents. We don't know how they got them."
- "Several of our best customers suddenly switched to this new competitor."
The situation has become serious. The employee has had months to exploit whatever information they took. Customer relationships that took years to build are now at risk. Competitive advantages that defined your market position are being used against you.
But here's the critical problem: the evidence is gone.
In the six months since that first phone call, here's what typically happened to the devices and data that could have proven the theft:
- The employee's laptop was reassigned to a new hire and wiped clean
- The computer was reimaged, destroying all forensic artifacts
- IT recycled the device entirely to make room for new equipment
- Email retention policies deleted the messages
- Cloud storage logs expired and were purged from the system
- The employee's phone was reset to factory settings
Without the original devices, forensic reconstruction becomes extremely limited. We can sometimes piece together fragments to tell a story, but the smoking gun evidence, the definitive proof that would have existed six months ago, no longer exists.
When the Bill Comes Due
Instead of a $5,000 investigation, the company is now facing a very different financial reality.
Legal fees for litigation typically range from $25,000 to $50,000 just to get started. Discovery costs, including depositions, document review, and subpoenas, add another $20,000 or more. Expert witnesses to analyze whatever evidence remains can cost $10,000 to $30,000. And if the case goes to trial, costs can easily exceed $100,000 to $200,000.
But the worst part isn't the money. It's that even after spending all of that, you still may not have definitive proof. Litigation without smoking gun evidence is risky. Opposing counsel knows exactly where your evidence gaps are. They'll argue that the similarities between your business and their client's new venture are coincidental. They'll claim that any information their client has was developed independently.
The emotional toll at this stage is significant. Business owners describe feeling:
- Frustrated that they didn't act when they had the chance
- Angry that someone they trusted would betray them
- Scared about the future of their business
- Exhausted from months of stress and worry
We hear the same sentiment repeatedly: "We spent ten years building this business, and now they're using everything we created." The fear of losing customers, losing market position, and potentially losing the company itself becomes very real. We have hear business owner after business owner explain how physically ill and emotionally drained they are because of these situations. Time and time again, owners say “I wish I had taken your advice”.
What Early Action Looks Like
Let's rewind to that first phone call and consider a different timeline.
If the investigation had proceeded immediately after the employee's resignation, here's what would have happened:
Step 1: Forensic analysis within days of departure
The employee's laptop and phone are secured before any data can be overwritten. A forensic image is created, preserving every bit of data exactly as it existed at that moment.
Step 2: Evidence identification
The analysis reveals specific artifacts: USB device connections with timestamps, files transferred to external drives, documents uploaded to personal cloud accounts, emails forwarded to Gmail, browser history showing visits to file-sharing sites.
Step 3: Attorney engagement
A detailed forensic report is provided to your attorney, documenting the evidence with proper chain of custody for court admissibility.
Step 4: Immediate legal action
Your attorney sends a demand letter or cease-and-desist notice, citing specific evidence of data theft. The former employee is put on notice that their actions have been documented.
Step 5: Injunction if necessary
If the employee has already started using your proprietary information, your attorney can file for a temporary restraining order or preliminary injunction to stop the damage immediately.
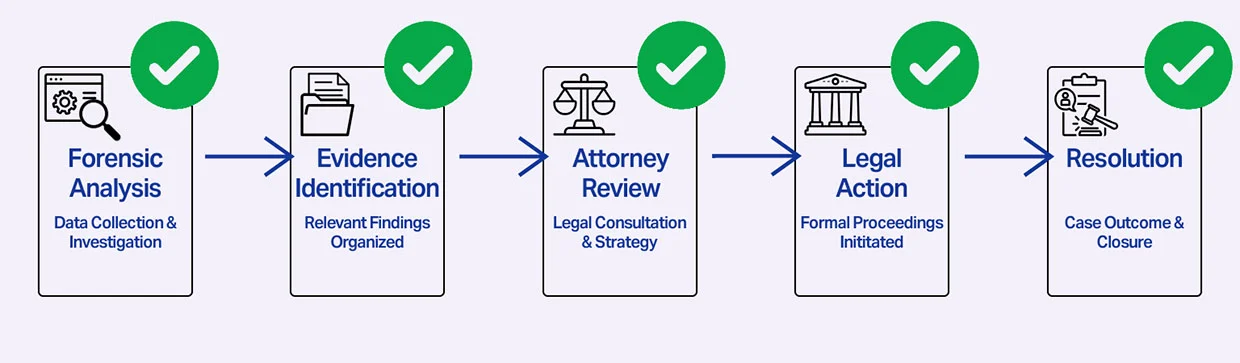
The results of this approach are dramatically different:
- Damage is minimized before it can spread to customers or markets
- Evidence is preserved with forensic integrity that will stand up in court
- Legal leverage is established immediately, while the employee is still vulnerable
- Resolution often happens quickly because the opposing party faces immediate consequences
Understanding the Risk
Not every departing employee poses the same risk. Understanding who qualifies as a "key employee" helps you prioritize when an employee data theft investigation makes sense.
Employees with the highest risk profile include:
- Sales staff who have direct relationships with customers and access to client lists
- Executives, Directors, and Key Employees who know strategic plans, financial data, and market positioning
- Engineers and developers who have access to source code, technical specifications, and proprietary processes
- Product managers who understand roadmaps, competitive analysis, and pricing strategies
- Anyone with access to trade secrets that provide competitive advantage
The pattern we see repeatedly is that data theft often precedes departure. According to research by Biscom, over 25% of employees steal proprietary data when leaving a company. The theft typically occurs in the days or weeks before resignation, when the employee knows they're leaving but still has full access to systems.
This is why traditional IT offboarding, while necessary, isn't sufficient. Standard offboarding typically includes:
- Disabling login credentials
- Recovering company devices
- Revoking cloud access permissions
What IT offboarding does NOT do:
- Examine what happened in the weeks before departure
- Recover deleted files or browser history
- Analyze USB device connections and file transfers
- Review email forwarding rules that were set up months ago
- Check for cloud storage synchronization that occurred before the exit
IT offboarding secures your systems for the future. An employee data theft investigation looks at what happened in the past. Both are necessary for complete protection.
How Expert Forensics Changes the Outcome
At Black Dog Forensics, we've conducted hundreds of employee data theft investigations. We understand the patterns, the artifacts, and the urgency of these situations.
Our approach includes:
- Forensic imaging with court-admissible standards, ensuring that any evidence we find can be used effectively in legal proceedings
- Data exfiltration analysis that identifies exactly what was taken, when, and how
- Insider threat investigations that go beyond the obvious to uncover sophisticated methods of data theft and current employees who might still be involved
- Expert reports that translate technical findings into clear, actionable intelligence for attorneys and business leaders
- Litigation support including expert testimony when cases proceed to court
What sets Black Dog Forensics apart is our ability to respond rapidly to time-sensitive situations. We understand that every day that passes increases the risk of evidence loss. Our team can often begin the forensic imaging process within hours of receiving the call.
Most importantly, we communicate clearly. Digital forensics is technical work, but our reports are written for business leaders and attorneys, not just other forensic experts. We explain what we found, what it means, and what options you have for moving forward.
Early forensic analysis protects businesses from irreversible damage. The evidence we preserve in those first critical days often becomes the foundation for successful legal action. More importantly, it provides the clarity you need to make informed decisions about how to protect your business.
The True Cost of Uncertainty
If there's one lesson we've learned from years of conducting these investigations, it's this: waiting rarely saves money. It usually multiplies costs exponentially.
When employees with access to sensitive data resign or are terminated, you have a small window to understand what happened. That window is measured in days, not months. The forensic artifacts that can prove or disprove data theft begin degrading immediately after departure.
The $3,500 to $5,000 investment in a forensic analysis provides:
- Peace of mind if the investigation finds no evidence of wrongdoing
- Actionable evidence if theft occurred, giving you legal options while they still exist
- Clarity about what you're actually facing, rather than months of uncertainty
In nearly every case where a business owner delayed the employee data theft investigation, they eventually say the same thing: "You were right. I wish we had done this six months ago."
The cost of waiting is almost always greater than the cost of knowing. When you suspect a departing employee may have taken company data, the time to investigate is now. Not because you're paranoid. Not because you distrust your employees. But because protecting your business requires acting while the evidence still exists.
The $5,000 decision seems expensive until you understand what the $100,000 problem looks like. We've seen it hundreds of times. The businesses that act quickly preserve their options. The businesses that wait often find themselves with neither evidence nor recourse.
If you're facing a departing employee situation and something doesn't feel right, trust that instinct. The call you make today could save you from the call you'll regret six months from now.
Black Dog Forensics assists companies and legal counsel with forensic reviews of departing employee devices to identify potential data exfiltration and preserve evidence when necessary.




 346-200-6097
346-200-6097




