Why Employee Departures Create a High-Risk Window for Data Theft

When a key employee leaves, most companies conduct an exit interview, disable the employee's login credentials, and move on. What many organizations fail to realize is that the most significant risk often occurs in the days and weeks before the employee resigns.
Employee departures are routine. People change jobs, retire, or pursue new opportunities. But data theft during departures is far more common than most companies realize. The executives, engineers, and sales leaders who drive your business forward often have access to sensitive intellectual property, customer relationships, and strategic plans that competitors would pay dearly to obtain.
Most companies invest considerable resources in HR exit processes. They conduct interviews, collect badges, and process final paychecks. Yet they routinely ignore the digital exit risks that can cost them hundreds of thousands of dollars in litigation, lost business, and damaged competitive position.
Here is the financial reality: A forensic review costing $3,500 to $5,000 could prevent six-figure litigation expenses down the road. When viewed as an insurance policy against one of the most vulnerable moments in your organization's lifecycle, the investment becomes obvious.
This article explains why companies should conduct digital forensic reviews of computers and digital assets when key employees leave. We will cover who qualifies as a key employee, how data theft typically occurs, why standard IT offboarding misses critical evidence, and what a proper forensic review entails.
What is a "key employee"?
Let us be clear: Not every departing employee needs a forensic review. The administrative assistant who spent six months with your company and had limited system access probably does not warrant this level of scrutiny.
A key employee is someone who has meaningful access to sensitive business information or operational knowledge that could damage your organization if misused. This is not about suspicion or accusations. It is about recognizing that certain roles carry inherent risk based on the access they require to perform their jobs.
Key employees typically have access to:
- Intellectual property and trade secrets proprietary algorithms, product designs, manufacturing processes, or research and development data
- Customer lists and pricing information detailed client databases, contract terms, pricing strategies, and sales pipelines
- Strategic business plans expansion plans, acquisition targets, market analysis, and competitive intelligence
- Proprietary processes or systems internal workflows, operational methodologies, and efficiency optimizations
- Sensitive financial information revenue projections, cost structures, profit margins, and investor communications
- Vendor relationships supplier contracts, negotiated rates, and supply chain configurations
The risk formula is straightforward: Access plus Opportunity. An employee with extensive access to sensitive information who is leaving for a competitor or starting a competing business has both the means and the motive to take information. This does not mean they will, but the combination creates a risk that prudent organizations should address.
The tone here is important. We are not accusing departing employees of theft. Most employees leave with integrity intact. But the risk is real, and the consequences of ignoring it can be severe.
Why departing employees present a unique digital risk
Employee departures represent the highest-risk moment for data exfiltration. Understanding why requires looking at both the practical and psychological factors at play.
The most common scenario involves employees preparing to join competitors. They rationalize that the client relationships they built or the expertise they developed belongs to them. They tell themselves they are not really stealing, just taking what is rightfully theirs. This self-deception makes the theft easier to justify.
Other employees actively download files before leaving. They may be planning to start competing businesses or simply want insurance against future disputes. Some take client lists and sales pipelines, believing these relationships are portable assets. Others copy proprietary processes, thinking they can replicate your success elsewhere.
Personal motivations vary. Resentment over perceived mistreatment can drive retaliatory data theft. Financial pressure creates opportunity-based theft. The belief that they are undercompensated for their contributions leads some to view data as backpay they are owed.
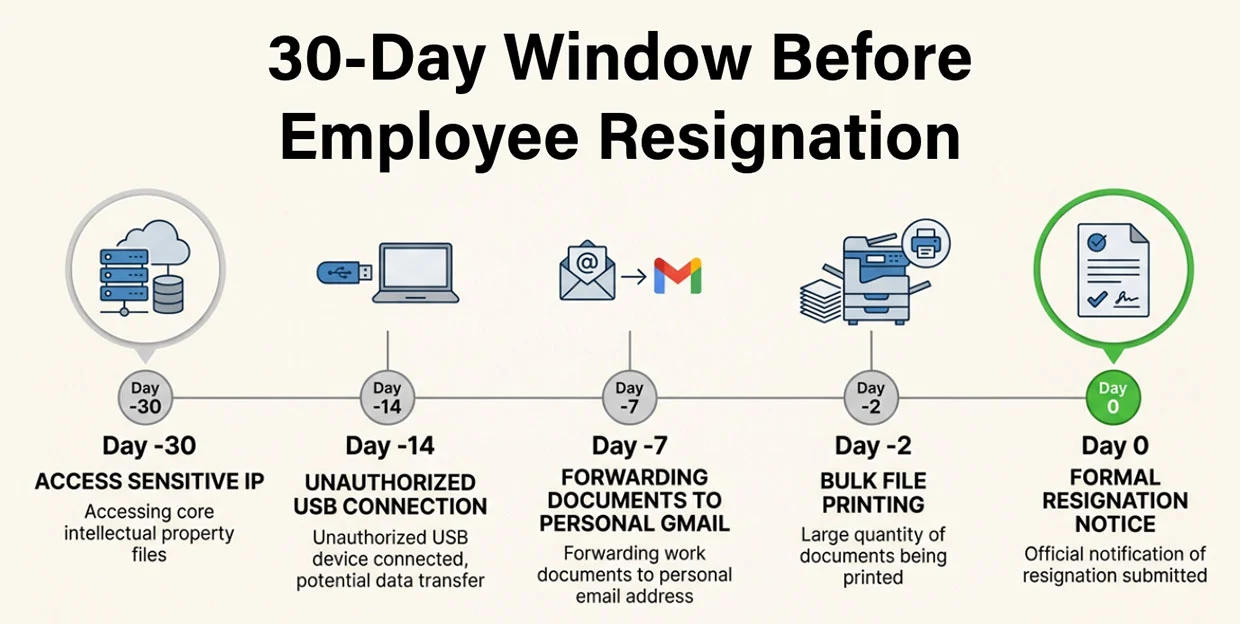
The statistics paint a sobering picture. Trade secret theft frequently involves former employees. Industry research consistently shows that a significant percentage of intellectual property theft occurs when employees leave organizations. Many incidents occur within 30 days of resignation, when access is still active but the employee has mentally checked out.
The critical insight: The majority of intellectual property theft occurs before the employee even walks out the door. By the time you are conducting that exit interview, the damage may already be done.
The five most common ways employees remove company data
Understanding how data exfiltration occurs helps explain why forensic reviews are necessary. Here are the five most common methods employees use to remove company information before departing.
1. Personal email forwarding
The simplest method is often the most common. Employees forward documents to personal Gmail, Outlook, Yahoo, or other email accounts. This is frequently done in bulk during the final days of employment, with employees sending dozens or hundreds of files to accounts they control outside your network.
The problem is that standard email monitoring often misses this activity. Employees may use personal webmail interfaces rather than desktop clients, bypassing some monitoring systems. They may compress files to avoid size limits or detection. And once the files leave your network, you have no visibility into what was taken.
2. USB drives and external hard drives
Despite being low-tech, USB drives remain extremely common tools for data theft. A $20 flash drive can hold thousands of documents. An external hard drive can hold your entire file server. Large volumes of data can be copied in minutes, often without triggering alerts.
Most organizations do not actively monitor USB device connections or track what files are copied to external storage. Even when policies prohibit personal USB devices, enforcement is often lax. The physical nature of this exfiltration method makes it particularly difficult to detect after the fact unless a forensic image has been obtained.
3. Cloud storage accounts
Dropbox, Google Drive, OneDrive, iCloud, and dozens of other cloud services make it trivial to sync company files to personal accounts. Employees install these applications on work computers, select folders to sync, and your proprietary data begins flowing to servers outside your control.
Cloud storage is particularly insidious because it can be set up once and continue operating automatically. An employee might configure syncing weeks before departure, allowing data to flow continuously without ongoing action. After they leave, the cloud account typically still contains everything that was synced.
4. Printing or exporting sensitive reports
Sometimes the oldest methods are the most effective. Employees print client lists, financial models, proprietary documents, and strategic plans. They export databases to spreadsheets. They take screenshots and photographs of sensitive information. They walk out with physical documents that leave little to no digital trail.
Physical removal of information is particularly difficult to detect because it often mimics legitimate work activity. Employees print documents as part of their jobs. The challenge is distinguishing legitimate printing from data theft, especially after the employee has departed.
5. Mobile phone synchronization
Corporate email and files synced to personal smartphones and tablets create significant exposure. Employees access company email on personal devices, download attachments, and retain access to sensitive communications long after departure. Files stored on mobile devices may not be wiped when employment ends.
Mobile device management (MDM) solutions can help, but many organizations either do not implement them or grant exceptions for convenience. On top of that, MDM solutions often break down with the phone operating system updates. Personal devices often fly under the radar of corporate security programs, making them attractive targets for data exfiltration.
The key point: Many of these activities leave digital artifacts that forensic analysis can identify. Sharing data often creates log entries. Cloud sync leaves log various artifacts. Email forwarding generates server records and local cache records. The evidence exists, but you need forensic expertise to find it.
Real-world impact: a business owner's experience
To understand how common this problem is, consider this post from a business owner on Reddit:
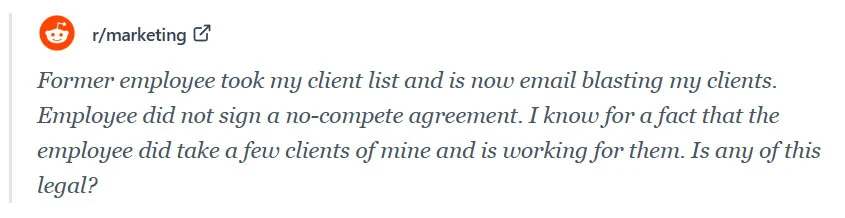
This illustrates several critical points. First, small businesses are particularly vulnerable. They often lack the legal protections (like non-compete agreements) that larger companies have in place. Second, the financial impact is immediate and real: active client poaching, lost revenue, and competitive damage. Third, many business owners are unsure of their legal options when this happens.
The Reddit post represents countless similar situations playing out across businesses every day. The question is not whether this can happen to you. The question is whether you will be prepared when it does.
Why standard IT offboarding often misses the problem
There is an important distinction between IT offboarding and digital forensics. Understanding this difference explains why so many data theft incidents go undetected.
Typical IT offboarding follows a predictable pattern:
- Disable user accounts and revoke system access
- Collect company-issued laptops and mobile devices
- Wipe or reimage devices for the next employee
- Archive email accounts according to retention policies, typically not done
- Reset shared passwords the employee may have known, again typically not done
These steps are necessary and appropriate. They protect against ongoing unauthorized access and prepare systems for new users. But they completely miss evidence of data exfiltration that occurred before the employee left.
Here is what standard IT offboarding misses:
Deleted files in unallocated space. When files are deleted, they are not immediately erased from the viewable area of the hard drive. The space they occupied is marked as available, but the data remains recoverable until overwritten. Forensic tools can recover these deleted files days, weeks, or sometimes even months after deletion.
USB connection history. Windows and macOS maintain records of USB devices that connected to the computer. Forensic analysis can identify when devices were connected, what files were accessed during those connections, and sometimes even the unique identifiers of the specific USB devices used.
Cloud sync activity. Cloud storage applications maintain local databases of synchronized files. Forensic review can reconstruct what was synced, when it occurred, and which cloud accounts received your data.
Email forwarding evidence. Email servers and client applications retain records of messages sent, including forwarding activity. Forensic analysis can identify bulk forwarding to personal accounts that might otherwise go unnoticed.
File access timelines. Operating systems track when files were created, modified, accessed, and often when deleted. Timeline analysis can reveal suspicious patterns, such as accessing years-old files in the days before departure or copying large numbers of files to unusual locations.
The fundamental distinction: Traditional IT processes focus on restoring systems for the next employee. Digital forensics focuses on preserving and analyzing evidence. IT departments are trained to maintain systems and support users, not to conduct investigative analysis. They lack the specialized tools and training required for forensic examination much less the ability to testify as an expert if need be.
What a digital forensic review actually looks for
A proper digital forensic review is methodical and thorough. It goes far beyond simply looking through file folders. Here is what the process involves.
Device imaging
The first step is creating a forensic image of the computer, an exact bit-by-bit copy of the entire storage device. This image is a perfect replica that cannot be altered, preserving the exact state of the system at the time of collection.
Forensic imaging is essential because it protects the integrity of the evidence. Any analysis is performed on the image, not the original device. This means the original evidence remains pristine and can be presented in court if necessary. It also allows multiple experts to examine the same data independently.
Timeline reconstruction
Forensic experts analyze what files were accessed, copied, or deleted and when these activities occurred. By building a chronological picture of user activity, they can identify suspicious patterns.
Timeline analysis might reveal that an employee accessed dormant project files they had not touched in years, copied large numbers of documents to external locations, or deleted significant volumes of data in their final days. These patterns tell a story that individual data points cannot.
External device activity
USB drive connections and file transfers leave traces in system logs and registry artifacts. Forensic analysis can identify when external storage devices were connected, what files were accessed during those connections, and potentially even identify the specific devices used.
This analysis can reveal whether an employee copied your customer database to a personal USB drive or transferred proprietary files to an external hard drive before returning their laptop.
Email and cloud transfers
Forensic review identifies suspicious outbound activity, including bulk email forwarding and cloud storage synchronization. Experts can reconstruct what data was transferred, when it occurred, and where it went.
This analysis might reveal that an employee forwarded emails to a personal Gmail account or synced your product development folder to their personal Dropbox.
Deleted data recovery
Even files the employee attempted to remove can often be recovered. When files are deleted, the data typically remains on the drive until overwritten by new data. Forensic tools can scan unallocated space and recover deleted files, sometimes revealing what the employee was trying to hide.
The goal of this entire process is threefold: Identify potential misconduct, document activity with precision, and preserve evidence in a form that can support legal action if necessary.
The cost comparison: prevention versus litigation
The financial case for forensic departure reviews is compelling. Let us look at the numbers.
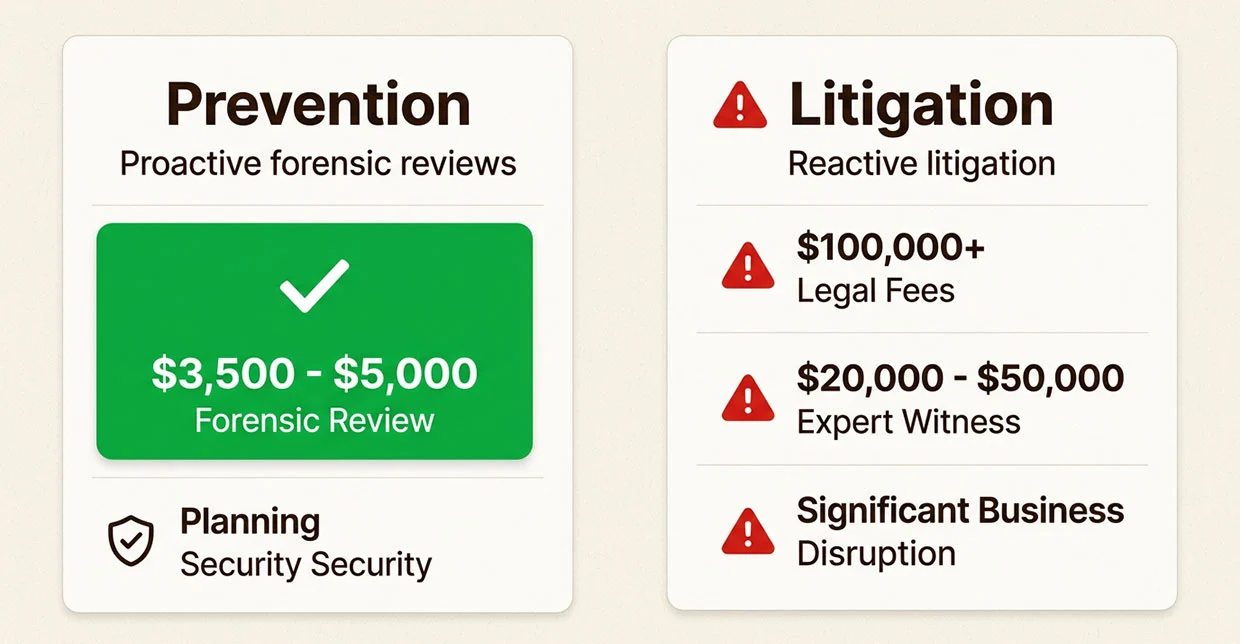
A forensic departure review typically costs between $3,500 and $5,000. This includes device imaging, analysis, and a comprehensive report documenting findings. For a senior executive or key technical employee with access to critical intellectual property, this is a modest investment.
Litigation, by contrast, routinely costs $100,000 or more. Complex cases involving significant damages can run into seven figures. These costs include attorney fees, discovery expenses, court costs, and the time value of executive attention diverted to legal proceedings.
Expert witness fees add another $20,000 to $50,000 or more. If you end up in litigation, you will need forensic experts to testify about what they found, how much your business is worth, and what the total loss due to the employees action is. Having conducted a proper forensic review at departure gives you this expertise ready to deploy to take immediate legal action and prevent further business loss.
Business disruption is harder to quantify but often the most significant cost. Litigation distracts leadership from running the business. Relationships with clients and partners may be damaged. Morale suffers. The competitor who obtained your trade secrets gains advantage in the marketplace.
The insurance analogy is apt. Companies carry liability insurance, property insurance, and cyber insurance to protect against risks that might never materialize. A forensic departure review serves a similar function, providing protection against one of the most vulnerable moments any organization faces.
A modest forensic review provides early visibility into potential risks and may prevent costly litigation later. In many cases, the review reveals nothing improper occurred, giving everyone peace of mind. In others, early detection allows organizations to address issues quickly before they escalate.
When companies should conduct a forensic departure review
Not every departure warrants forensic review. Here is practical guidance for deciding when to invest in this protection.
Executive departures. C-level executives, vice presidents, directors, and senior managers typically have broad access to strategic information, financial data, and sensitive relationships. Their departures should always trigger consideration of forensic review.
Engineers and developers. Technical employees often have access to source code, product designs, technical architectures, and innovation roadmaps. When engineers leave for competitors or to start competing ventures, forensic review is strongly advised.
Sales leaders with client lists. Sales executives and account managers have relationships and knowledge that competitors value highly. Their departure to competing organizations creates significant risk of client poaching and trade secret theft.
Employees joining competitors. The risk increases dramatically when an employee leaves to join a direct competitor. The combination of access to your information and position at a competitor creates obvious conflicts.
Suspicious behavior prior to resignation. Unusual activity in the weeks before departure, such as accessing files outside normal responsibilities, working odd hours, or exhibiting secretive behavior, may warrant investigation.
Terminations involving disputes. When employment ends on contentious terms, the risk of retaliatory data theft increases. Employees who feel wronged may be motivated to take information as payback.
A simple risk assessment framework: Consider the sensitivity of information the employee accessed, the circumstances of their departure, and their destination. High scores on any of these dimensions suggest forensic review is warranted.
The value of having documentation before a dispute
There are significant strategic advantages to conducting forensic reviews before disputes arise.
Knowing what actually happened. Speculation about data theft is corrosive. It poisons relationships, creates anxiety, and leads to poor decisions. A forensic review provides clarity and facts. Either the employee took something or they did not. Knowing the truth allows you to respond appropriately.
Avoiding unnecessary accusations. Without forensic evidence, companies sometimes make accusations that cannot be substantiated. This damages reputations, creates legal exposure, and destroys relationships unnecessarily. A forensic review either provides evidence to support action or confirms that no action is needed.
Preserving evidence properly. If evidence of misconduct exists, it must be preserved in a forensically sound manner to be admissible in court. Conducting a proper review at departure ensures evidence is preserved correctly from the start.
Supporting legal counsel. If litigation becomes necessary, having a forensic report prepared by qualified experts gives your attorneys the evidence they need to easily initiate litigation and build a strong case. Starting from scratch after a dispute arises is more expensive and less effective.
Making informed decisions. With forensic findings in hand, leadership can make rational decisions about how to proceed. Options might include doing nothing, sending a preservation letter, negotiating a resolution, or pursuing litigation. Each option can be evaluated based on actual evidence rather than suspicion.
The power of facts versus speculation cannot be overstated. In many cases, companies discover that nothing improper occurred. The departing employee acted with integrity, and the forensic review provides peace of mind. In other cases, early detection allows organizations to address issues quickly before they escalate into major problems.
Protecting your company with proactive digital forensics
Employee departures are inevitable. People move on. Careers evolve. Organizations change. But data loss does not have to be an inevitable consequence of departure.
A digital forensic review provides clarity and protection during one of the most vulnerable moments for any organization. It transforms uncertainty into knowledge, speculation into evidence, and risk into managed exposure.
Just as companies carry insurance to protect against unforeseen risks, a digital forensic review serves as a form of protection during the departure of a key employee. The $3,500 to $5,000 investment is modest compared to the potential costs of undetected data theft.
The question is not whether you can afford to conduct forensic reviews of departing key employees. The question is whether you can afford not to.
Black Dog Forensics assists companies and legal counsel with forensic reviews of departing employee devices to identify potential data exfiltration and preserve evidence when necessary. Our team brings decades of experience in digital forensic investigations, expert testimony, and litigation support. When a key employee departs, we help you know what happened and protect what matters.




 346-200-6097
346-200-6097




