Why Timing Matters in Digital Evidence Seizures and Searches

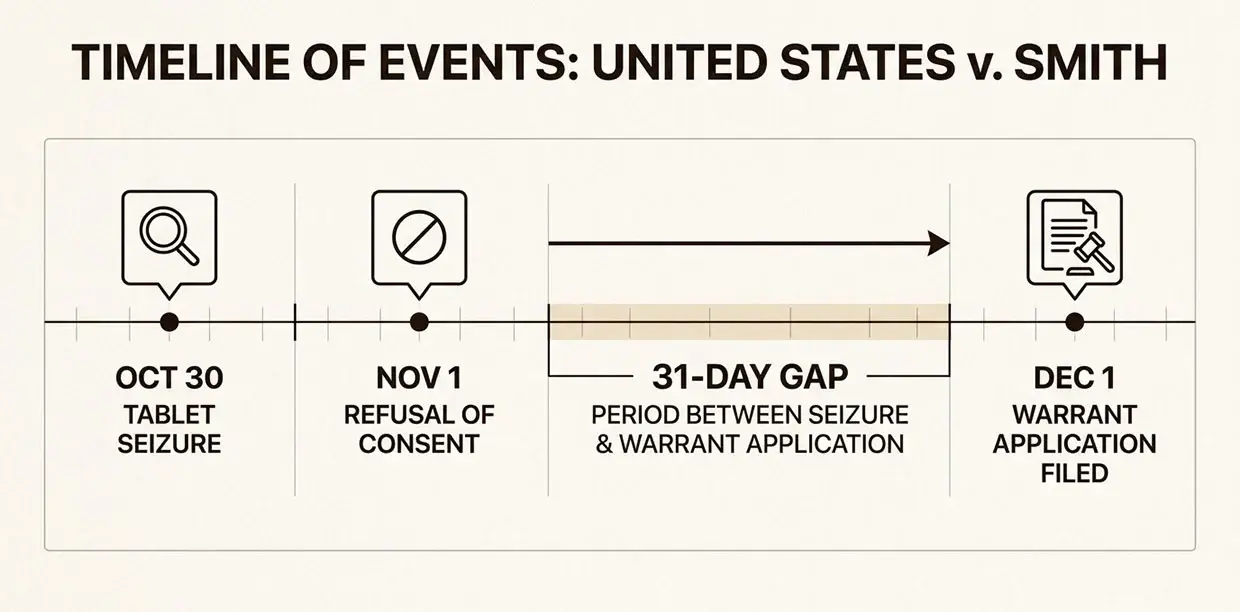
Modern criminal investigations increasingly rely on digital evidence from phones, tablets, and electronic devices. As law enforcement adapts to this reality, courts are now confronting how Fourth Amendment protections apply to the seizure and search of these devices. The Second Circuit's decision in United States v. Smith, No. 17-2446 (2d Cir. 2020), offers a significant ruling on this issue. The court held that waiting 31 days to seek a warrant to search a seized tablet violated the Fourth Amendment. Yet despite this constitutional violation, the evidence was not suppressed. This outcome creates important implications for both legal strategy and digital forensic analysis.
Case Background
The case began on October 30, 2014, when a New York State Police trooper encountered a vehicle pulled off the side of a rural road in Keene, New York. The driver, Kirkland Smith, was unconscious behind the wheel with the engine running. After removing Smith from the vehicle, the trooper searched the car for identification and noticed a Nextbook tablet on the front passenger seat.
According to the officer's deposition statement completed that same day, the tablet screen displayed what appeared to be child pornography.
The trooper seized the tablet immediately, though by the time it was secured, the screen had turned off and the image was no longer visible. Smith was arrested for driving while intoxicated. The next day, an investigator visited Smith's home seeking consent to search the tablet, which Smith declined. Despite this refusal, police retained custody of the device. They waited 31 days before applying for a search warrant on December 1, 2014. The subsequent search revealed dozens of videos and images of child pornography, which led to additional search warrants for Smith's residences where more illegal material was found.
Smith was indicted on federal charges and moved to suppress the evidence, arguing that the delay in seeking the warrant violated his Fourth Amendment rights. The district court denied the motion, and Smith entered a conditional guilty plea while preserving his right to appeal. The Second Circuit ultimately affirmed the conviction but issued a significant ruling on the constitutional question.
The Key Fourth Amendment Issue: Delay in Seeking a Warrant
The Fourth Amendment requires that when police lawfully seize property with probable cause, they must act with diligence in obtaining a search warrant. The Supreme Court has consistently held that temporary seizures are constitutional only when police diligently seek judicial authorization within a reasonable time. As the Second Circuit noted, even a seizure based on probable cause becomes unconstitutional if police act with unreasonable delay in securing a warrant.

In analyzing whether the 31-day delay was reasonable, the court applied a four-factor test:
- Length of delay: The court gave independent weight to this factor, concluding that a month-long delay "well exceeds what is ordinarily reasonable." The delay here was nearly three times longer than an eleven-day delay the Second Circuit had previously considered at the edge of reasonableness.
- Importance of the property: The court emphasized that tablet computers and similar devices implicate heightened privacy concerns. Citing Riley v. California, the opinion noted that modern electronic devices contain "tax records, diaries, personal photographs, electronic books, electronic media, medical data, records of internet searches, banking and shopping information." This vast quantity of deeply personal data distinguishes digital devices from ordinary personal effects.
- Property interest: Smith did not consent to the seizure or relinquish control of the tablet. While the existence of probable cause entitled police to seize the device temporarily, it did not diminish Smith's underlying property interest beyond what was necessary to seek a prompt warrant.
- Justification for delay: The district court had found that the investigator was solely responsible for 24 active criminal investigations across an expansive rural area. However, the Second Circuit rejected this justification, noting that "the general press of police business may not justify a lengthy delay absent particular evidence showing why other police duties reasonably took precedence." The record showed very little investigative activity on Smith's case during the 31-day period.
Balancing these factors, the majority concluded that the delay violated the Fourth Amendment. This holding is significant because it confirms that digital devices cannot be held indefinitely without judicial authorization, even when police have probable cause for the initial seizure.
Why the Evidence Was Still Allowed
Despite finding a Fourth Amendment violation, the court declined to apply the exclusionary rule, which would have suppressed the evidence. The exclusionary rule is not an automatic remedy for every constitutional violation. Under Herring v. United States, suppression is appropriate only when police violate the Constitution deliberately, recklessly, or with gross negligence, or when the violation results from recurring or systemic negligence.
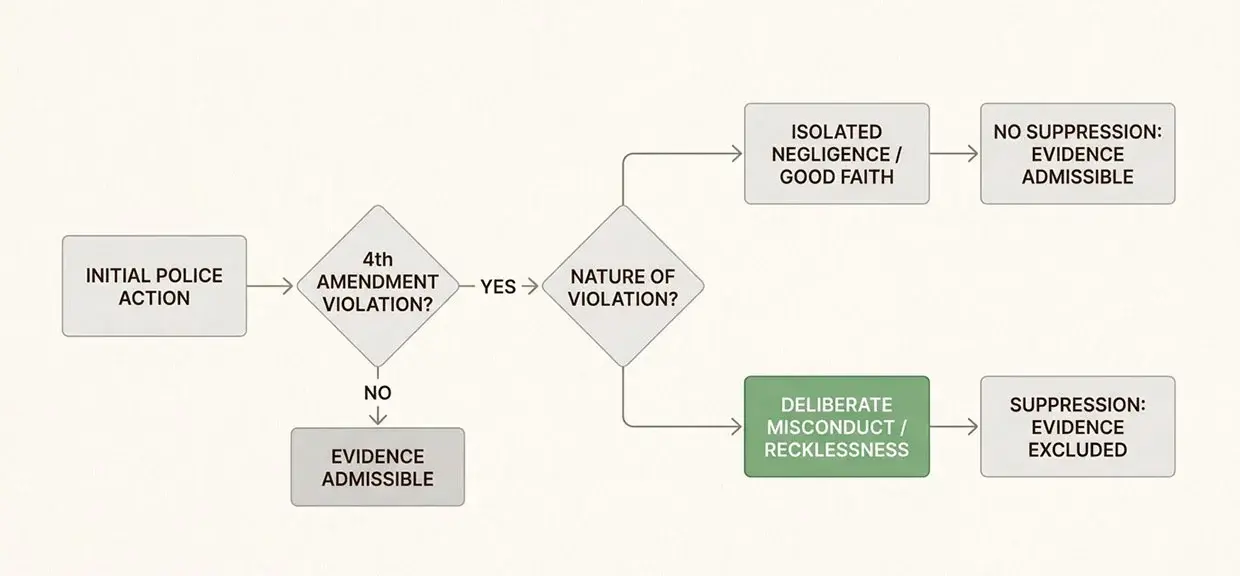
The court found that the investigator's conduct amounted to "isolated negligence" rather than deliberate misconduct. The delay did not afford police any strategic advantage, and there was no evidence of systematic or recurring delays by the officer or his agency. The majority characterized the delay as an "isolated act of negligence" that, while constitutionally problematic, did not warrant the deterrent effect of suppression.
The court also considered whether an objectively reasonable officer would have known the delay violated the Fourth Amendment. Noting that precedent on this issue was mixed, with some courts upholding similar or longer delays, the majority concluded that a reasonable officer might not have known with certainty that 31 days was unconstitutional. The opinion emphasized, however, that going forward, a month-long delay would ordinarily be deemed unreasonable, and the principles articulated in the decision would guide future application of the exclusionary rule.
Judge Kearse concurred in the judgment but wrote separately to express her view that the delay was not unreasonable. She emphasized the investigator's heavy caseload and noted that Smith never requested the return of his tablet. Her concurrence highlights the difficulty defendants face in persuading courts that law enforcement has acted improperly.
The Digital Forensic Perspective
Courts often rely heavily on officer testimony about how digital evidence was discovered. In Smith, the trooper testified that he observed potential child pornography on the tablet screen without unlocking the device. This testimony formed the basis for the probable cause finding that justified both the initial seizure and the subsequent warrant application.
However, digital devices frequently contain artifacts that can objectively reconstruct what actually happened during an encounter. Unlike physical evidence, where observations are often limited to officer testimony, electronic devices maintain detailed logs of system events that can corroborate or contradict official accounts.
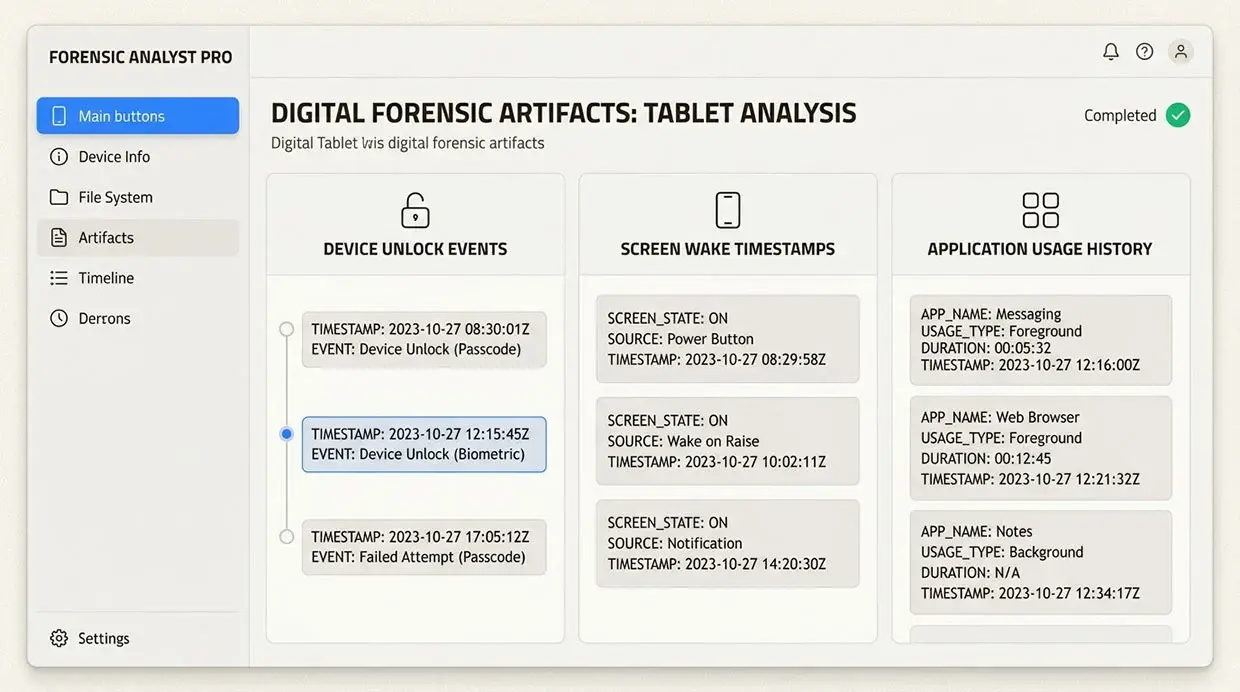
Forensic analysis can reveal:
- Device unlock events: Timestamps showing when the device was unlocked, including method (PIN, pattern, biometric)
- Screen wake events: Records of when the display activated and what application was visible
- Application usage logs: Which apps were opened, when, and for how long
- File access timestamps: When specific files were last accessed, modified, or viewed
- System logs: Comprehensive records of device state changes and user interactions
These artifacts can reveal whether a device was unlocked, navigated, or interacted with during an encounter, providing objective evidence independent of officer testimony.
Why Forensic Analysis Could Matter in Cases Like This
The officer in Smith testified that the image was visible without unlocking the tablet. From a forensic standpoint, this raises technical questions. Modern tablets and smartphones rarely display stored images on locked screens. While some devices show notifications or limited previews, accessing actual image files typically requires unlocking the device first.
If forensic artifacts showed the device was actually unlocked or manipulated by law enforcement before the seizure was documented, several serious legal issues could arise:
- Plain view doctrine: If officers unlocked the device to view its contents, the plain view doctrine might not apply. The doctrine permits warrantless seizures of contraband observed in plain view during lawful police activity, but it does not authorize police to conduct warrantless searches to reveal concealed evidence.
- Warrantless search: Manipulating a device to unlock it or navigate to specific content could constitute a warrantless search, violating the Fourth Amendment, regardless of what was ultimately discovered.
- False statements in warrant affidavits: If forensic evidence contradicts the officer's testimony about how the image was observed, the warrant affidavit could potentially contain false or misleading statements necessary to establish probable cause.
This scenario could trigger a challenge under Franks v. Delaware and form the basis for a suppression motion attacking the validity of the warrant. A Franks motion allows a defendant to seek suppression when law enforcement officers knowingly or recklessly include false statements in a warrant affidavit that are necessary to establish probable cause. To prevail, the defense must show not only that the statement was false, but that the officer made the statement deliberately or with reckless disregard for the truth.
The Importance of Showing Bad Faith
The exclusionary rule analysis in Smith highlights a critical point: the remedy is more likely to apply when police conduct involves deliberate misconduct, reckless disregard for the truth, or knowingly false statements. Isolated negligence, even when it results in constitutional violations, will not typically trigger suppression.
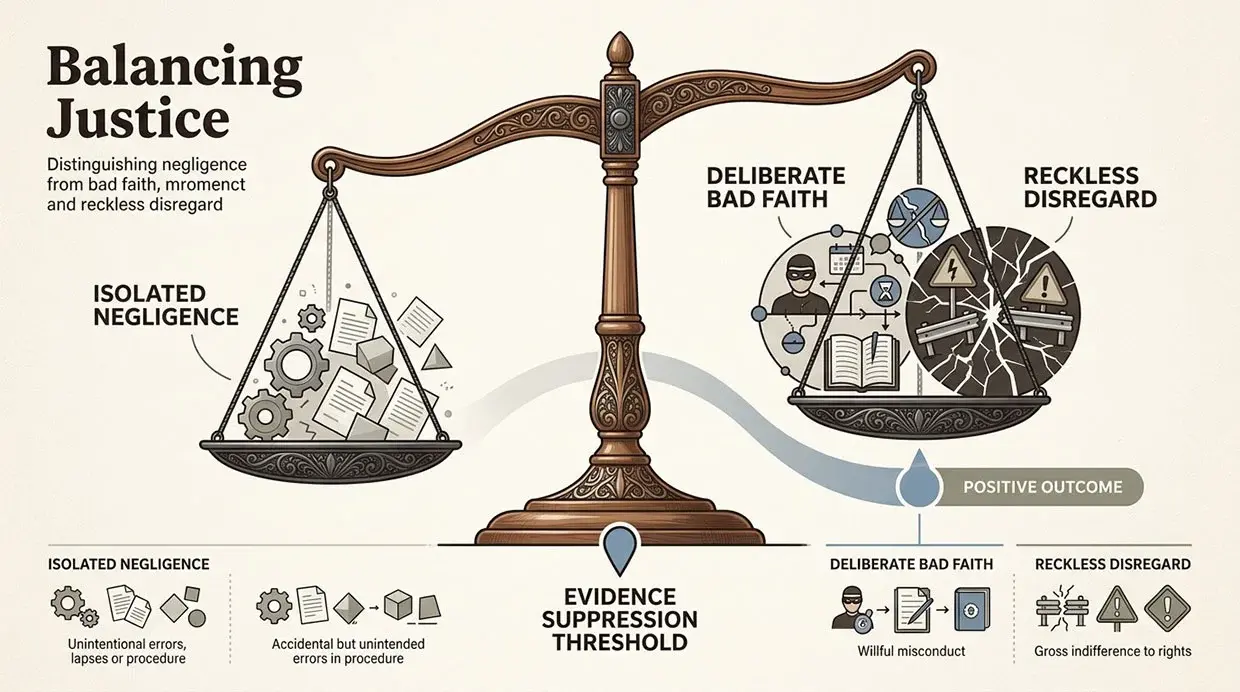
If forensic evidence demonstrated that officers:
- Manipulated the device to unlock it without authorization
- Navigated through applications or files beyond what was visible on the screen
- Inaccurately described what occurred during the encounter
This could establish bad faith rather than simple negligence. In that scenario, suppression of the evidence becomes much more likely. The forensic analysis transforms the case from one involving an unfortunate procedural delay to one involving potential deliberate constitutional violations.
The Smith court's reliance on the absence of "strategic advantage" also suggests that cases where officers gain an investigative edge through constitutional violations would be viewed differently. If forensic analysis reveals that officers unlocked a device and discovered evidence before obtaining a warrant, the strategic advantage is clear, and the exclusionary rule would more naturally apply.
Takeaways for Attorneys
Defense attorneys handling cases involving digital evidence seizures should consider several practical steps:
- Document the timeline: Establish exactly when the device was seized and when the warrant was requested. Calculate the days elapsed and identify any investigative steps taken during that period.
- Request forensic examination early: Engage a qualified digital forensics expert to examine the device for artifacts that may contradict officer testimony about how evidence was discovered.
- Analyze the warrant affidavit: Compare the officer's sworn statements with what is technically possible on the device in question. Look for inconsistencies between the described observations and the device's actual capabilities.
- Consider Franks challenges: If forensic analysis reveals discrepancies, evaluate whether a Franks motion challenging the warrant's validity is appropriate.
- Challenge the exclusionary rule analysis: Even if a Fourth Amendment violation is established, be prepared to argue that the violation was not merely negligent but involved deliberate or reckless conduct warranting suppression.
Early forensic analysis can sometimes reveal issues that significantly impact suppression arguments. The objective evidence contained within digital devices often tells a different story than officer testimony, and uncovering that evidence can be crucial to protecting a defendant's constitutional rights.
Digital Evidence Analysis from Black Dog Forensics
United States v. Smith demonstrates two important realities in modern digital investigations. First, delays in seeking warrants for seized devices can violate the Fourth Amendment, particularly when the seized property contains the vast quantities of personal data typical of modern tablets and smartphones. Second, evidence may still be admitted unless the defense can demonstrate deliberate misconduct or bad faith rather than isolated negligence.
Digital forensic analysis can play a crucial role in determining what actually occurred during an investigation and whether officer testimony aligns with the objective evidence contained within the device itself. At Black Dog Forensics, we specialize in uncovering the digital artifacts that reveal the true story behind the evidence. Our forensic examinations can identify device unlock events, application usage patterns, and system logs that may support or challenge the official account of how digital evidence was discovered.
When the constitutional protections of the Fourth Amendment are at stake, objective forensic analysis can make the difference between evidence being admitted or suppressed. If you are handling a case involving digital evidence seizure and need expert forensic analysis, contact Black Dog Forensics to discuss how we can help uncover the facts that matter.
Reference Link: 31 Day Delay - US v. Smith - 17-2446-2020-07-28




 346-200-6097
346-200-6097




