How to Assess Whether Sensitive Client Data Was Accessed

"I think someone accessed my email… are my clients' tax records exposed?"
During tax season, this is one of the most dangerous questions a CPA can face.
Depending upon the firm, email accounts can be the central hub for client communications, tax documents, Social Security numbers, and financial records. At the very least it often contains this information. If someone gains access, the issue is not just security. It is whether sensitive client data was exposed, and whether you now have an obligation to act.
This guide explains how to determine what happened, what forensic evidence can reveal, and why the first 24 to 48 hours are critical.
Why email compromise is a serious risk for CPAs
Your email often contains everything an identity thief needs. Tax returns, W-2s, 1099s, Social Security numbers, bank account details, and years of client communications. During tax season, when email volume peaks and deadlines create urgency, attackers know you are distracted.
Email breaches expose sensitive tax documents and personal identifiers, creating significant legal and financial liabilities for accounting firms.
The IRS reported nearly 200 tax professional data incidents potentially affecting up to 180,000 clients. Many of these began with a single click on a phishing email.
Consider what happened to Salling Madeley, PLLC, an Austin-based accounting firm. In February 2024, a part-time employee received an email that looked like a routine password reset reminder. It was busy season. She clicked. Within hours, hackers had accessed the firm's portal and were downloading client files.
The firm's managing partner, Catharine Drake Madeley, put it plainly: "Why would a hacker target a tax firm? Because they want tax data."
The financial impact can be devastating. According to The Tax Adviser, forensic discovery, remediation, and reporting typically cost between $70,000 and $300,000. State and federal reporting requirements, plus credit monitoring for affected clients, can add another $100,000 to $300,000.
That does not include ransomware demands, which have ranged from $100,000 for small firms to $2.6 million for large practices.
If your firm handles sensitive client data, breach investigations should be part of your incident response planning before an incident occurs.
What attackers actually do inside a compromised email account
Once inside your email, attackers do not sit idle. They act quickly and methodically.
Here is what they typically do:
- Search for keywords. Attackers run searches for terms like "tax return," "SSN," "W-2," "refund," and "bank account" to find high-value documents.
- Access sent items. Years of outbound emails contain a goldmine of historical client data.
- Impersonate you. They may email your clients requesting additional information, wire transfers, or updated documents.
- Set rules to hide communications. Attackers set rules to hide incoming email from specific addresses so that you do not see active communication.
- Set forwarding rules. Attackers configure rules to forward all incoming email to an external address, giving them ongoing access even after you change your password.
- Download attachments. PDFs of tax returns, scanned W-2s, and client intake forms are prime targets.
- Determine financial accounts. Attackers will look for emails from other business management systems to determine if they can reset your password and gain access to those accounts.
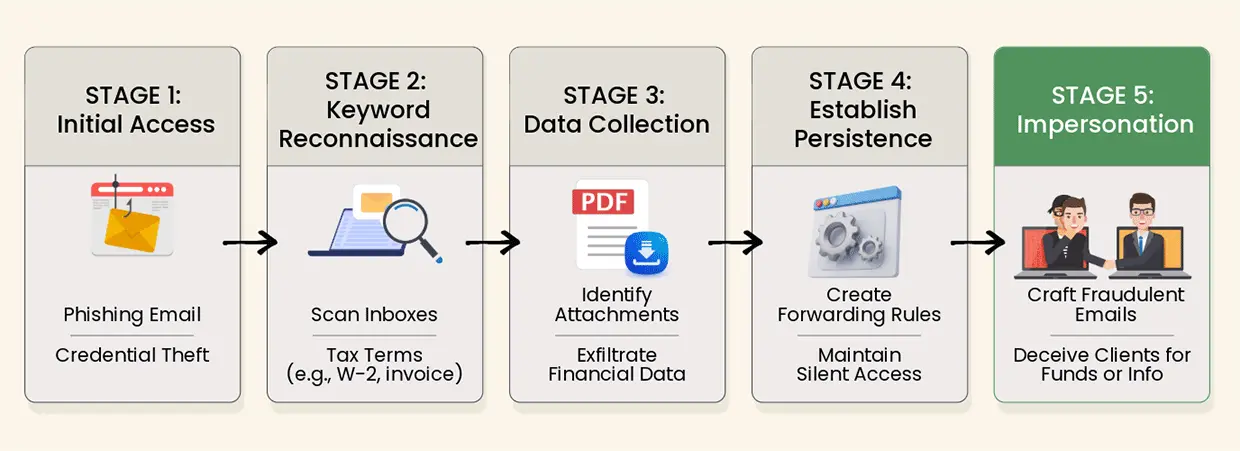
Understanding the methodical progression of a Business Email Compromise attack helps forensic investigators identify exactly where and how data was compromised.
This is Business Email Compromise (BEC), and it is often more dangerous than simple phishing. While phishing tries to steal credentials, BEC exploits the trust your clients have in you. A message that appears to come from their CPA requesting "updated bank information for a refund" is likely to get a response.
According to Kroll's research, email compromise accounted for nearly 46% of incident response engagements in 2024.
Understanding what attackers do helps forensic investigators know where to look. Our email and document authentication services can help determine if communications have been tampered with or spoofed.
The question that matters most: What did they access—and what did they take?
When you discover a potential breach, the question is not "was I hacked?"
The question is: "What did they access, and what did they take?"
This distinction matters because your legal and professional obligations depend on the answer. Here is what you need to determine:
- Which emails were viewed? Certain access logs might show if an attacker opened specific messages.
- Were attachments downloaded? Download activity leaves forensic traces.
- Which client communications were exposed? The scope of affected clients determines notification requirements.
- Was data forwarded externally? Forwarding rules and outbound email logs reveal if information left your systems.
The difference between "an attacker accessed your email" and "an attacker downloaded client tax returns" is the difference between a security incident and a reportable data breach.
In most jurisdictions, the obligation to notify is not triggered by unauthorized access alone. It is triggered by whether sensitive personal information was actually exposed or acquired.
If you suspect data theft, forensic analysis can determine the scope of what was taken.
Privacy and legal considerations
Data breach laws are a patchwork of state and federal regulations. Understanding your obligations requires knowing which laws apply to your firm.
State breach notification laws: Currently, 46 states plus the District of Columbia, Guam, Puerto Rico, and the Virgin Islands have security breach notification laws. Some require notification to affected individuals. Others require notification to state attorneys general. The timing varies, with some states requiring notification within as few as five days.
Crucially, the law that applies is based on where your clients live, not where your firm is located. If you have clients in multiple states, you may need to comply with multiple notification regimes.
Texas example: Under the Texas Identity Theft Enforcement and Protection Act, breach notices must be made to affected individuals and the Texas attorney general within 60 days after determining that a breach involving sensitive personal information has occurred.
Federal requirements: The FTC Safeguards Rule, enforced under the Gramm-Leach-Bliley Act, applies to tax preparers. It requires businesses to develop a written information security plan describing their program to protect customer information.
The IRS requires all tax professionals with preparer tax identification numbers (PTINs) to affirm that their organization has a "written security plan in place" to protect client data.
Professional liability: Beyond regulatory obligations, you face potential claims for damages. Clients can bring direct claims for costs incurred to investigate and mitigate damages, including forensic services, public relations expenses, and credit monitoring. Cross-claims may arise if your clients face lawsuits from their employees or customers.
Given the complexity, consulting with legal counsel experienced in data breach response is essential.
For comprehensive guidance on cybersecurity and data breach investigations, working with experienced forensic professionals can help ensure you meet all regulatory requirements.
The biggest mistake CPAs make after a breach
The most common mistake? Resetting the password and assuming the problem is solved.
This approach fails on multiple levels:
- It ignores historical access. Changing your password stops future access, but does nothing to reveal what the attacker already did.
- It relies on assumptions. Without forensic analysis, you are guessing at the scope of exposure.
- It wastes critical time. Digital evidence has a shelf life, and every day that passes makes reconstruction harder.
As one risk management specialist noted: "By the time many firms realize the scope of an incident, the evidence needed to understand it is already gone."
There is also a critical distinction between IT remediation and forensic investigation. Your IT provider's job is to stop the bleeding: shut down access, remove malware, restore systems. A forensic investigator's job is to understand what happened: establish a timeline, identify what data was accessed, and document findings in a court-admissible format.
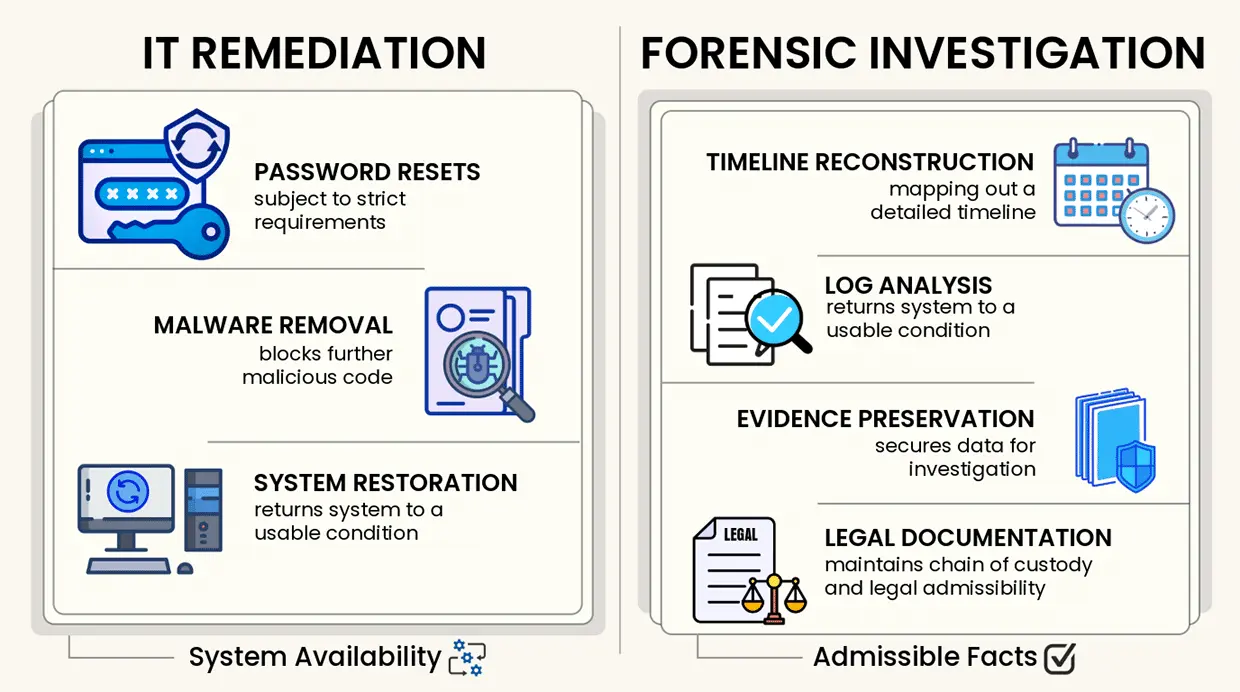
Forensic investigators provide the critical evidence needed to meet legal reporting requirements, whereas IT teams focus primarily on restoring operations.
Both roles are important, but they are not the same. Relying solely on your IT provider to investigate a potential data breach is like asking your mechanic to determine fault in a car accident. They can fix the car, but they are not trained to reconstruct the crash.
Where digital forensics comes in
Digital forensics can answer the questions that matter most after a suspected breach.
Here is what a forensic investigation can determine:
- How access occurred. Was it a phishing email? A credential stuffing attack? A compromised third-party integration? Understanding the entry vector helps prevent recurrence.
- Timeline of activity. When did the attacker first gain access? How long were they in the system? What did they do during that time?
- Emails accessed or searched. Email logs can reveal which messages were opened, which folders were accessed, and what search terms were used.
- Downloads and exfiltration. Forensic analysis can identify whether attachments were downloaded and whether data was forwarded to external addresses.
- Persistence mechanisms. Attackers often create backdoors: forwarding rules, additional user accounts, or scheduled tasks. Forensics identifies and documents these.
The process follows rigorous protocols to ensure findings are court-admissible. This includes maintaining chain of custody, using validated forensic tools, and documenting every step.
At Black Dog Forensics, our forensic investigations and analysis services include detailed examination of email systems, cloud accounts, and user activity. Our user activity analysis can track digital behavior, logins, and file transfers to identify exactly what an attacker did.
Why timing matters: Digital evidence has a shelf life
Digital evidence does not last forever. In fact, in email systems, it can disappear faster than you think.
Most email platforms retain detailed access logs for only 30 to 90 days. After that, the granular data you need to reconstruct an attacker's activity may be gone forever. Cloud providers routinely overwrite logs as part of normal operations. Deleted emails may be purged from recycle bins after a set period. Even active accounts show only recent activity in standard admin panels.
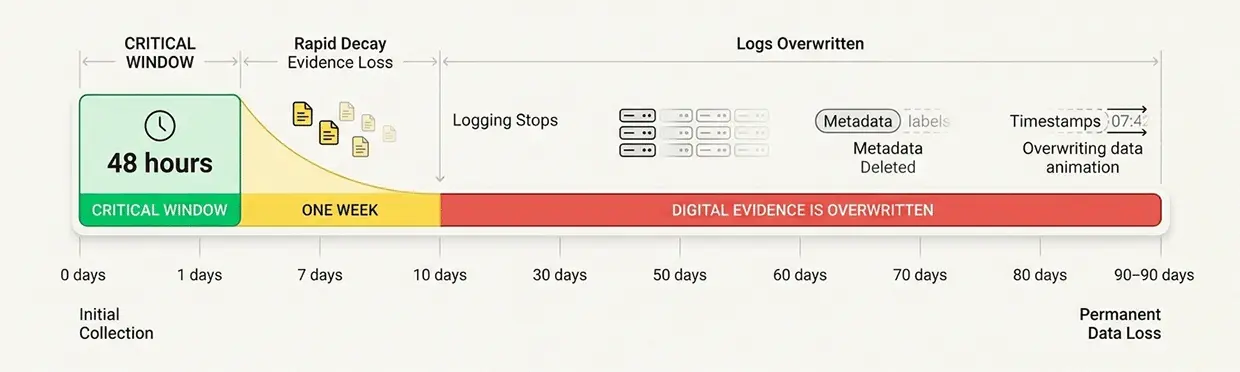
Acting within the first 48 hours is vital because server logs and digital footprints are often overwritten or purged within weeks.
This is why the first 24 to 48 hours after discovering a potential breach are critical. The actions you take (or fail to take) during this window can determine whether you ever understand what happened.
If you suspect a breach, immediate corporate forensic data preservation can secure evidence before it is overwritten or deleted.
What you should do immediately
If you suspect your email has been compromised, here are the steps to take:
- Secure the account. Change passwords immediately and enable multi-factor authentication (MFA) if it is not already active. Force logout of all active sessions.
- Engage a forensic expert early. The sooner a forensic investigator begins, the more evidence they can recover.
- Consult legal counsel. If sensitive data may have been exposed, legal guidance is essential for navigating notification requirements.
- Preserve logs and account data. Before making any other changes, capture email access logs, audit logs, and account settings. These may be overwritten if you wait.
- Do not rely solely on internal IT review. Your IT team can secure systems, but forensic investigation requires specialized expertise.
- Avoid altering or deleting data unnecessarily. Every change you make can overwrite evidence. Document any changes you must make.
- Follow the rules of your jurisdiction for reporting. Depending upon the jurisdiction of your clients, you may need to report to the attorney general’s office within days or other regulatory agencies.
If you need immediate assistance, get expert forensic assistance from our team.
Possible outcomes of a forensic investigation
A forensic investigation can yield several possible outcomes, each with different implications:
- No sensitive data was accessed. The attacker gained access but did not view or download client information. This is the best-case scenario, but it requires evidence to support and often still takes a risk-based approach to determine if a notification should occur, even though no evidence was located to determine if there was access to sensitive data.
- Limited exposure. The attacker accessed non-sensitive materials or a limited subset of client data. Notification obligations may be narrower.
- Confirmed access to sensitive data. Forensic evidence shows the attacker viewed or downloaded tax returns, SSNs, or financial documents. This triggers notification obligations.
- Evidence of data exfiltration. The attacker forwarded data to external systems. This is the most serious scenario and requires a comprehensive response.
Regardless of the outcome, clarity is valuable. Knowing what happened allows you to respond appropriately, meet your legal obligations, and protect your clients. Guessing leaves you exposed to both under-reaction and over-reaction.
Protecting your reputation and client trust
CPAs hold a unique position of trust. Clients entrust you with their most sensitive financial information. How you respond to a security incident can either reinforce that trust or destroy it.
Consider the CPA firm mentioned earlier. After their breach, they notified affected clients promptly, offered credit monitoring, and worked with clients to file legitimate returns quickly. The result? They did not lose a single client.
As the managing partner noted, "Most were appreciative that we responded quickly."
Transparency matters, but it must be informed transparency. Notifying clients before you understand the scope of a breach can create unnecessary panic. Delaying notification beyond legal deadlines can create liability. The key is to move quickly to understand what happened, then communicate clearly and accurately.
Proper incident response demonstrates professionalism. It shows clients that you take their data security seriously and that you have processes in place to handle crises.
At Black Dog Forensics, we understand the Black Dog Promise: to retrieve the truth with integrity and precision, giving you the clarity you need to move forward.
When to engage a forensic expert
The answer is simple: as early as possible.
Early engagement preserves evidence. It allows forensic investigators to capture logs before they are overwritten, image systems before they are modified, and establish a clear timeline while events are fresh.
When selecting a forensic expert, look for:
- Court-admissible methods. The investigation must follow protocols that ensure findings will stand up in legal proceedings.
- Experience with CPA firms. Understanding the specific risks and regulatory environment of accounting practices matters.
- Clear reporting. You need findings explained in plain language, not technical jargon.
- Rapid response. Evidence degrades quickly. Your forensic team should be able to mobilize immediately.
At Black Dog Forensics, we specialize in digital forensics for professional services firms. Our process is designed to provide clarity quickly, with documentation that meets legal standards.
Learn more about our team and our process to understand how we can help when every hour matters.
The difference between a contained incident and a reportable breach often comes down to one thing: what you do in the first 24 to 48 hours.
If you suspect your email has been compromised, do not wait to understand the full scope. Engage forensic expertise early, preserve evidence, and get the clarity you need to protect your clients and your practice.




 346-200-6097
346-200-6097




