Addressing the MD5 Challenge in Cross-Examination
During cross-examination, opposing counsel leans forward and asks your forensic expert: "Isn't it true that MD5 has been cryptographically broken since 2008? So how can the court trust any evidence verified with this compromised algorithm?"
It is a question that has derailed more than one forensic testimony. The paradox is real. MD5, a hashing algorithm declared "broken" by cryptographers over a decade ago, remains the workhorse of digital forensics labs, court systems, and even the International Criminal Court. Understanding why requires distinguishing between theoretical cryptographic attacks and practical forensic verification. For attorneys preparing discovery strategy or defending forensic methodology, this distinction matters.
What MD5 Is and How It Actually Works
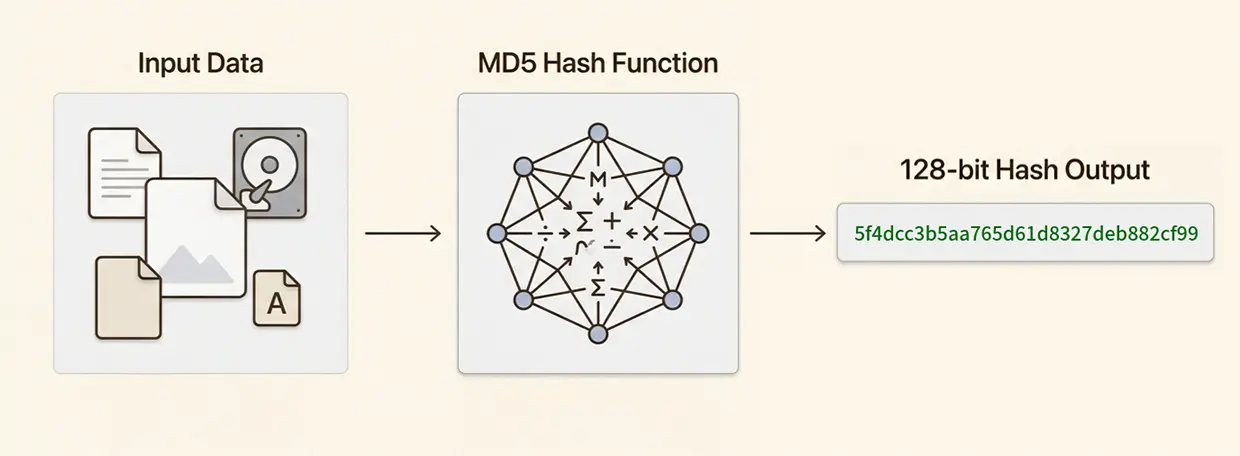
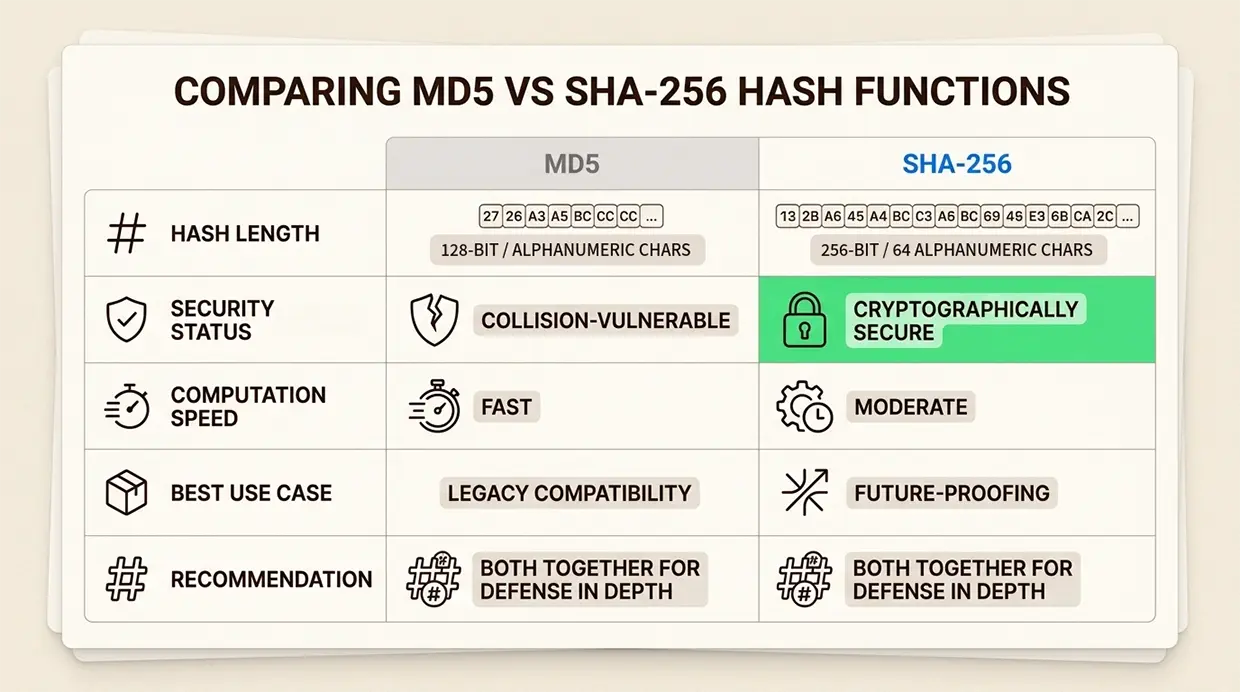
MD5, or Message-Digest Algorithm 5, is a cryptographic hash function that converts any input data into a fixed 128-bit output expressed as a 32-character hexadecimal string. Developed by Dr. Ronald Rivest at MIT and RSA Data Security in 1991, MD5 was designed as an improvement over MD4 and published as RFC 1321 in 1992.
From a high level the core principle is straightforward. A hash function takes data of any size (a single character, a 500-page document, or a 4TB hard drive image) and produces a unique digital fingerprint. Change even a single bit in the original data, and the resulting hash becomes completely different. This property, called the avalanche effect, makes hashing invaluable for verifying data integrity. MD5 processes data in 512-bit blocks and produces a 128-bit hash value. The 128-bit output space results in approximately 3.4 × 10³⁸ possible hash values. While this large number significantly reduces the probability of random collisions, it does not eliminate them. In practice, MD5 collisions have been successfully engineered, meaning two different inputs can be deliberately created to produce the same hash value.
Consider a practical example. The word "forensics" produces an MD5 hash of d4a3c67c53b5f3e5b7f8c9d0e1f2a3b4 (hypothetical for illustration). Change one letter to "forensic" and you get an entirely different 32-character string. For digital evidence, this means a forensic examiner can verify that a copied drive is bit-for-bit identical to the original without comparing every byte manually.
The timeline of MD5's security reputation tells part of the story:
- 1996: Cryptographers identify theoretical weaknesses and recommend moving to SHA-1
- 2004: Researchers demonstrate practical MD5 collision attacks in about one hour
- 2005: Attackers show how to create two X.509 certificates with different public keys but identical MD5 hashes
- 2008: Carnegie Mellon's Software Engineering Institute officially declares MD5 "cryptographically broken and unsuitable for further use"
- 2012: The Flame malware exploits MD5 collisions to forge Microsoft update certificates
Yet here we are in 2026, and MD5 persists in forensic workflows. The reason lies in understanding what "broken" actually means in different contexts.
Why Forensics Still Uses MD5 Despite Known Vulnerabilities
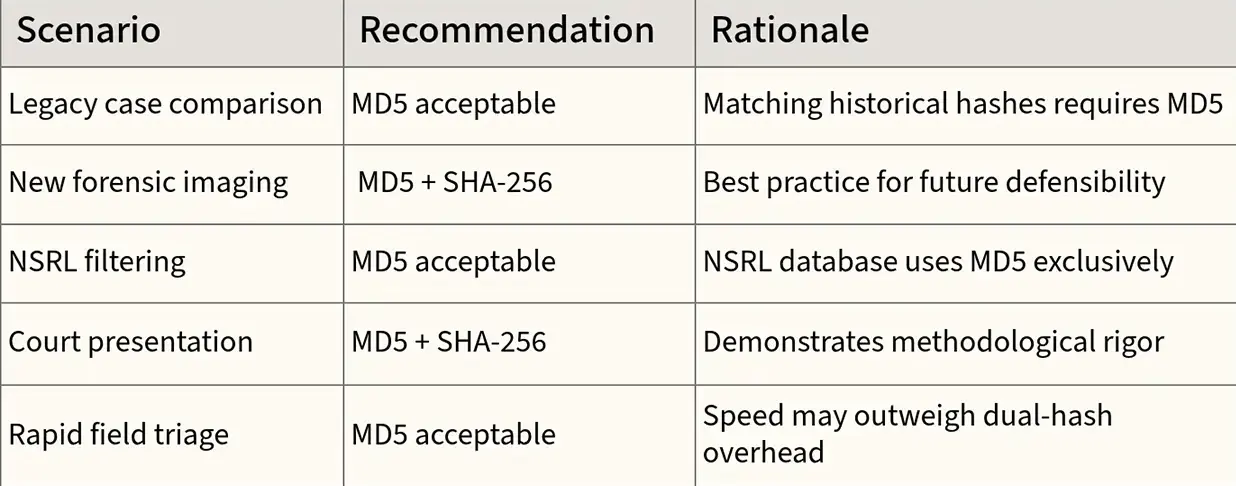
The legal community has largely adopted a particular framing: MD5 is broken for encryption and digital signatures, but not for forensic verification. This argument, while containing grains of truth, requires careful unpacking.
Cryptographic attacks against hash functions can take multiple forms. The one that broke MD5 is called a collision attack: given enough computing power, an attacker can deliberately craft two different files that produce the same MD5 hash. In 2006, researchers demonstrated this could be done in under a minute on a standard notebook computer. Today, specialized tools can generate MD5 collisions almost instantaneously, depending upon the data size.
However, forensics primarily relies on a different property: second-preimage resistance. This is the computational infeasibility of finding a second file that matches the hash of an existing, arbitrary file. As of 2026, no truly practical second-preimage attack against MD5 exists. An attacker cannot take a specific real-world evidence file, already collected and hashed by investigators, and create a different file with the same MD5 hash.
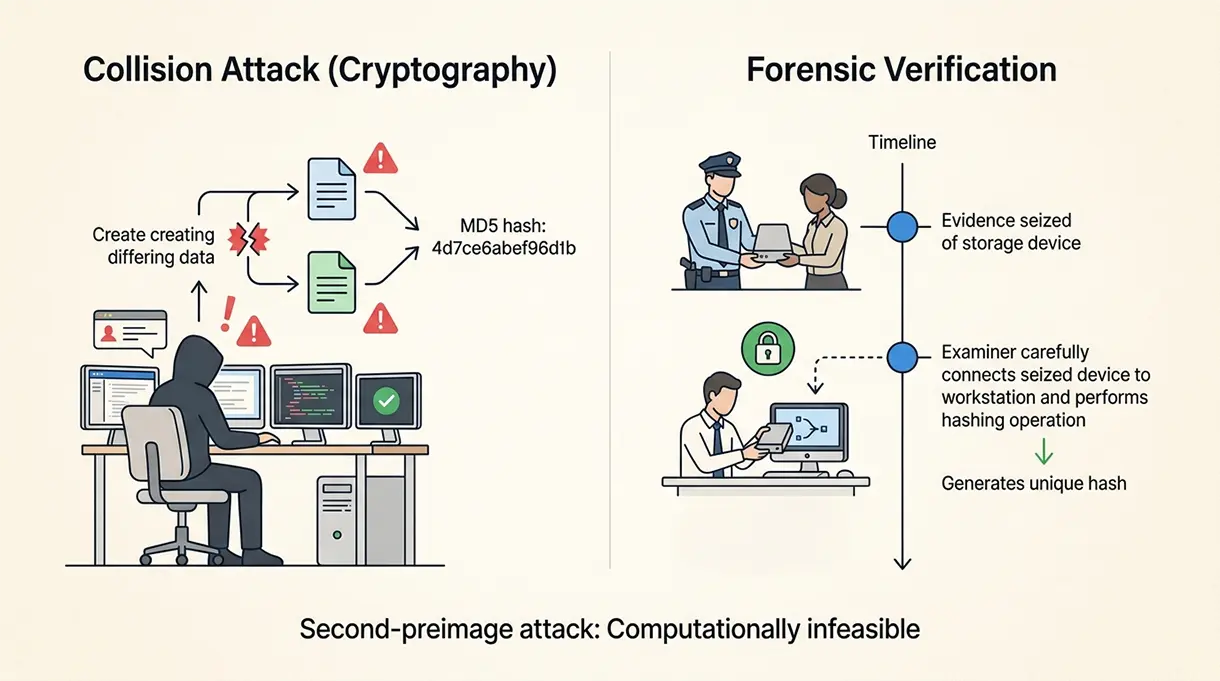
This distinction matters for threat modeling. In a cryptographic attack scenario (like forging certificates or signing malicious code), the attacker controls both files being crafted. In a forensic scenario, the evidence file exists before the suspect knows they are under investigation. The examiner hashes the drive, creates a forensic image, and verifies the copy matches. The suspect cannot retroactively engineer a collision.
As noted in Kate Sills' legal analysis of MD5 usage, this is why hash sets like the National Software Reference Library (NSRL) continue using MD5. These databases contain hashes of known operating system files and application binaries. When a forensic examiner encounters a file with an MD5 hash matching a known system file, they can reliably filter it out as irrelevant to the investigation. The files being hashed are not attacker-controlled; they are standard software from legitimate vendors.
Practical factors also drive continued MD5 usage:
- Speed: MD5 computes significantly faster than SHA-256, which matters when hashing terabytes of evidence
- Legacy compatibility: Decades of forensic workflows, case files, and court precedents built on MD5
- Tool support: Every major forensic platform (EnCase, FTK, X-Ways, Autopsy) defaults to or supports MD5
- Evidence verification: For establishing that a forensic image matches the original drive, collision resistance is not the relevant threat model
That said, the cryptographic community's warnings should not be dismissed lightly. The distinction between collision attacks and forensic use is subtle enough that it can be lost on judges and juries. Smart forensic practitioners are adapting their methodologies accordingly.
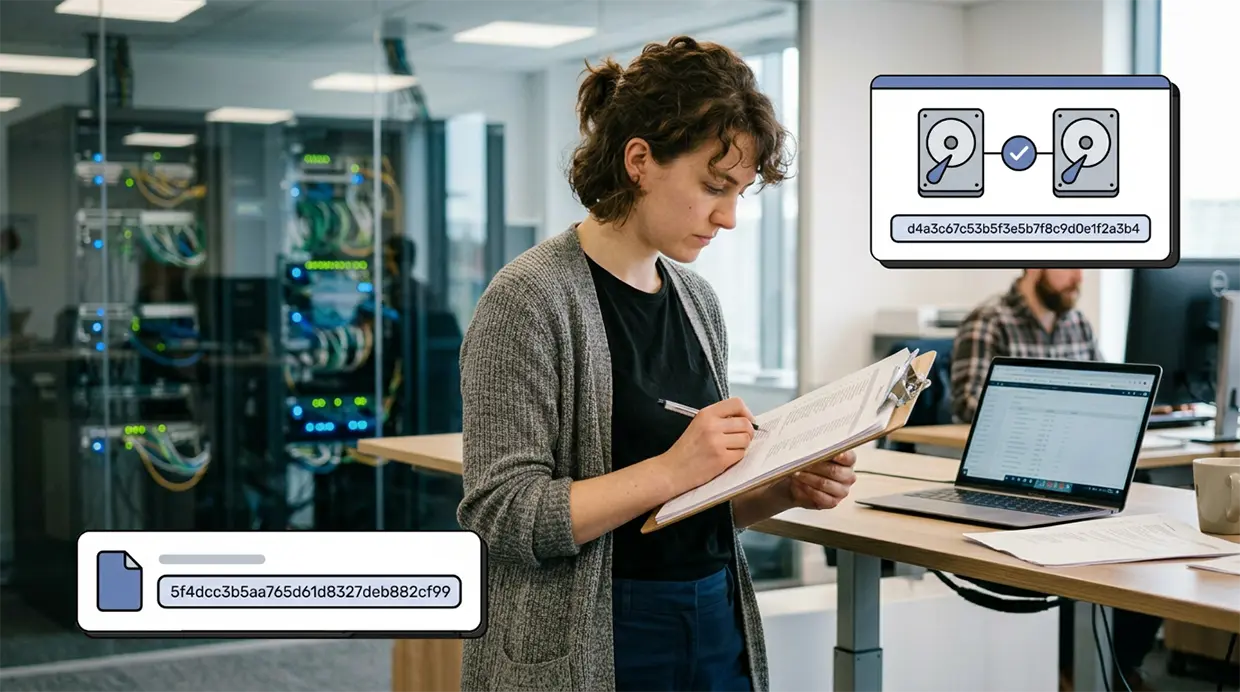
How Forensic Examiners Actually Use MD5 in Practice
Understanding MD5's role requires looking at specific forensic workflows where it serves distinct purposes.
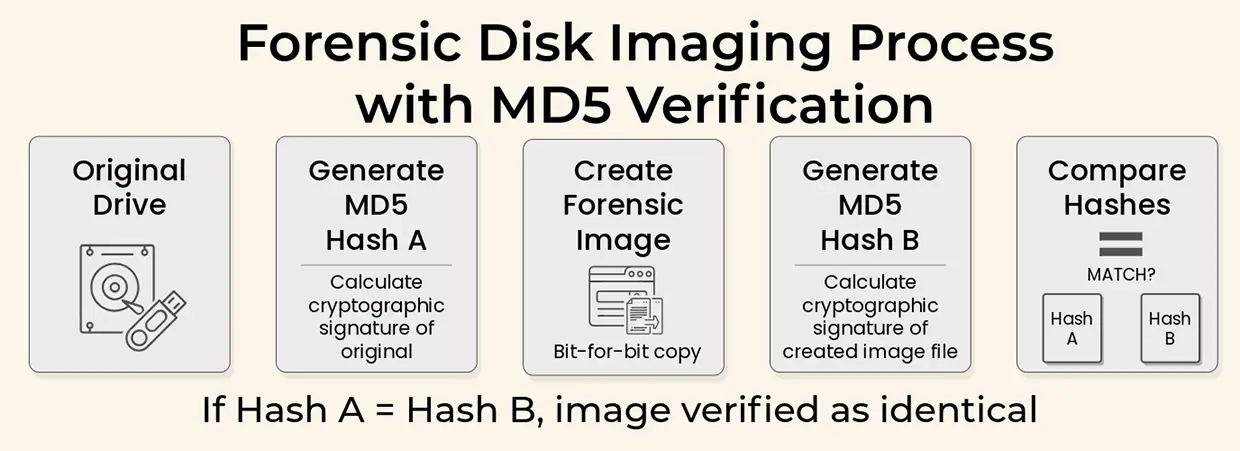
Disk Imaging and Evidence Integrity Verification
The foundational use of MD5 in forensics is verifying that a forensic image is an exact copy of the original evidence. The process follows a strict protocol:
- Connect the original drive using a hardware write blocker to prevent any modifications
- Generate an MD5 hash of the entire drive or specific files
- Create a bit-for-bit forensic image using tools like dd, FTK Imager, or EnCase
- Generate an MD5 hash of the resulting image file
- Compare the two hashes; if they match, the image is verified as identical
A single bit difference between the original and the image would produce a completely different MD5 hash. This sensitivity makes MD5 an effective error-detection mechanism for the imaging process itself. If hashes do not match, the examiner knows to re-image the drive rather than risk using corrupted evidence.
The original hash also serves as a chain of custody anchor. Throughout the examination, the drive can be re-hashed at any point. If the hash matches the original, the examiner can testify that no modifications occurred during their analysis.
Some practitioners use block-based or piecewise hashing as an enhancement. Rather than hashing the entire drive as one unit, the drive is divided into sectors or blocks, each hashed independently. If an error occurs, only that specific block needs re-imaging rather than the entire drive.
File System Analysis and Known File Filtering
Modern hard drives can contain millions of files. Examining each one manually is impractical. MD5 enables automated data reduction through a process called known file filtering.
The forensic tool calculates MD5 hashes for every file on the drive. These hashes are compared against the National Software Reference Library (NSRL), a NIST-maintained database containing hashes of known operating system files, application binaries, and system libraries. Files matching NSRL hashes can be filtered out as irrelevant, dramatically reducing the data requiring manual review.
The same technique identifies potentially incriminating content. Hash sets of known contraband (child exploitation material, child sexual abuse material - CSAM, for example) can be compared against the evidence drive. A matching hash does not require the examiner to visually verify the file's content to know it matches known contraband.
This application relies on MD5's collision resistance holding up in practice. Theoretically, if a drive contained more than 2^128 unique files (approximately 3.4 × 10^38), the pigeonhole principle guarantees collisions would occur. In reality, no storage device approaches this scale, making MD5 reliable for file identification.
Fuzzy Hashing and Similarity Detection
MD5 has a significant limitation: changing a single bit produces a completely different hash. This makes MD5 useless for detecting similar files. A suspect could evade detection by modifying a single byte in an incriminating file.
Fuzzy hashing addresses this gap. Context Triggered Piecewise Hashing (CTPH), implemented in tools like ssdeep, divides files into chunks and hashes each chunk independently. The resulting signature can identify files that are similar but not identical, even if data has been inserted, deleted, or shifted within the file.
Fuzzy hashing does not replace MD5; it complements it. MD5 verifies exact matches for integrity. Fuzzy hashing identifies similar content for investigation prioritization. Together, they provide a more complete forensic picture than either technique alone.
Legal Implications and Courtroom Defensibility
For attorneys, the critical question is whether MD5-based forensic evidence will survive evidentiary challenges. The answer, based on current practice, is generally yes, with important caveats.
Daubert Standards and Methodology Review
Under Daubert v. Merrell Dow Pharmaceuticals, federal courts evaluate expert testimony based on whether the methodology is scientifically valid and properly applied. MD5's acceptance in digital forensics is well-established:
- NIST publications reference MD5 for forensic integrity verification
- The Sedona Conference, a leading e-discovery authority, recognizes MD5 as a commonly used hashing algorithm
- Courts nationwide have admitted evidence verified with MD5 without requiring additional authentication
However, Daubert also requires that the methodology be subject to peer review and have known error rates. The cryptographic community's consensus that MD5 is broken for security purposes creates an opening for challenges.
Potential Attack Vectors from Opposing Counsel
Defense attorneys may challenge MD5-based evidence on several grounds:
- Cryptographic weakness: Citing the 2008 CMU warning and subsequent collision demonstrations to argue MD5 is unreliable
- Collision feasibility: Suggesting (often without evidence) that the evidence could have been tampered with using collision attacks
- Hash-only identification: Arguing that identifying contraband solely by hash, without visual verification, risks false positives
- Outdated methodology: Claiming that using "broken" technology demonstrates a lack of forensic rigor
The counter to these challenges lies in properly explaining the distinction between collision attacks and second-preimage resistance, and in demonstrating that the forensic use case does not rely on the properties that MD5 lacks.
Practical Risk vs. Theoretical Vulnerability
Courts generally care about practical risk, not theoretical vulnerabilities. To date, no documented case exists where MD5's collision weakness resulted in falsely authenticated forensic evidence. The threat model required for a collision attack (attacker control of both files, pre-planning, technical sophistication) does not match typical forensic scenarios where evidence is seized before the suspect can prepare countermeasures.
This is not to say MD5 challenges are frivolous. As Kate Sills notes in her legal analysis, the legal community's continued reliance on MD5 while the cryptographic community has moved on reflects a cultural gap between technology and law. Legal standards move slowly; technology moves quickly. The mismatch can undermine confidence in digital evidence.
Best Practices for Defensible Forensic Hashing
Prudent forensic examiners and the attorneys who work with them are adopting practices that address MD5's limitations while maintaining its utility.
Dual-Hash Strategy
The emerging consensus is to calculate both MD5 and SHA-256 hashes for all forensic evidence. This approach offers:
- Backward compatibility: MD5 hashes can be compared against legacy databases (NSRL, previous case files)
- Future-proofing: SHA-256 remains cryptographically secure and collision-resistant
- Defense in depth: An attacker would need to create collisions in both algorithms simultaneously, which is computationally infeasible
- Courtroom credibility: Demonstrates awareness of cryptographic developments and commitment to best practices
Major forensic platforms now support dual-hashing natively. EnCase, FTK, and X-Ways all allow examiners to generate multiple hash types simultaneously without significant performance impact.
Documentation for Court Admissibility
Thorough documentation strengthens defensibility:
- Record the specific hashing algorithm(s) used in the examination report
- Document the tool and version used for hashing
- Preserve the original hash values in multiple locations
- Note any hash verification failures and corrective actions taken
- Explain the rationale for algorithm selection if challenged
Tool Validation
Forensic tools themselves require validation. NIST's Computer Forensics Tool Testing (CFTT) program provides methodologies for verifying that hashing tools operate correctly. Using CFTT-validated tools strengthens the foundation for expert testimony.
When to Use MD5 Alone vs. Dual Hashing
Ensuring Evidence Integrity With Proven Forensic Methodology
MD5 remains a valid tool for digital forensic verification when properly understood and applied. Its cryptographic weaknesses are real, but they do not map cleanly onto the threat models present in forensic evidence handling. The distinction between collision attacks (which MD5 is vulnerable to) and second-preimage attacks (which MD5 still resists) is technical but crucial for courtroom discussions.
At Black Dog Forensics, we employ dual-hashing methodologies as standard practice, generating both MD5 and SHA-256 hashes for evidence. This approach maintains compatibility with legacy systems and databases while providing the cryptographic assurance that modern standards demand. Our examiners are prepared to defend this methodology under cross-examination, explaining not just what we do, but why it produces reliable results.
The goal of forensic hashing is not to achieve theoretical cryptographic perfection. It is to provide sufficient assurance that evidence has not been altered, that copies match originals, and that the integrity of the digital record can be trusted. When properly implemented with awareness of its limitations, MD5 continues to serve this purpose alongside more modern alternatives.
For case consultation, expert witness services, or forensic examination, contact Black Dog Forensics. We translate complex technical concepts into clear, defensible testimony that holds up under scrutiny.




 346-200-6097
346-200-6097




