The Cross-Examination Question Designed to Confuse Juries
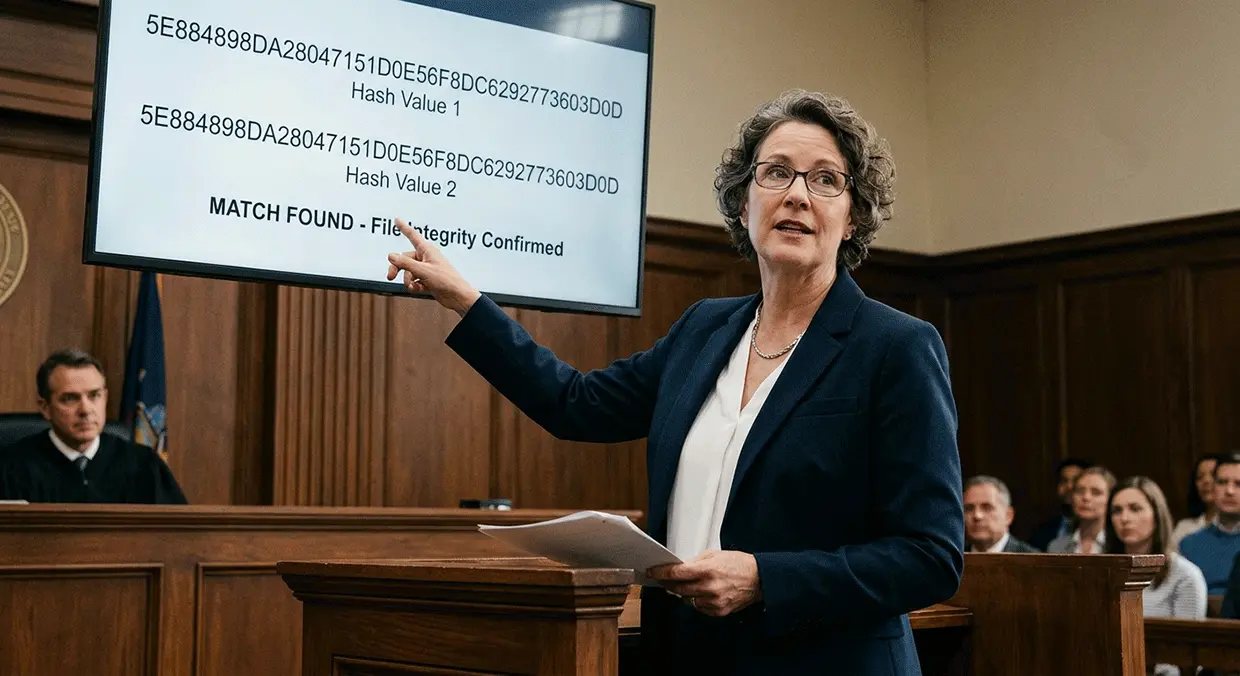
Picture this: you are on the witness stand, having just explained how you verified the integrity of critical evidence using MD5 hash values. The defense attorney approaches and asks, "Isn't it true that MD5 is cryptographically broken and can produce identical hashes for completely different files?"
The implication hangs in the air. If MD5 is "broken," how can the jury trust that your evidence has not been tampered with? How can the court rely on your analysis if the foundation of your integrity verification is compromised?
This question strikes at the heart of a widespread misconception about MD5 hash collisions. The short answer is this: while MD5 collision vulnerabilities are real and well-documented in cryptographic literature, they do not occur naturally in the wild for digital evidence collected on an investigative case. Every documented collision has been the result of deliberate engineering by researchers or sophisticated attackers with specific goals and significant resources. For forensic examiners and the attorneys who rely on their testimony, understanding this distinction is not just academic. It is essential for defending evidence integrity in court.
What MD5 Collisions Actually Are (And How They Differ From Preimage Attacks)
To understand the real risks, we must first understand what MD5 is and what it does. MD5, or Message-Digest Algorithm 5, is a hash function that produces a 128-bit hash value from any input data. Think of it as a digital fingerprint. Whether you are hashing a single text file or a 4-terabyte hard drive image, MD5 produces a fixed-length string of 32 hexadecimal characters that uniquely represents that data.
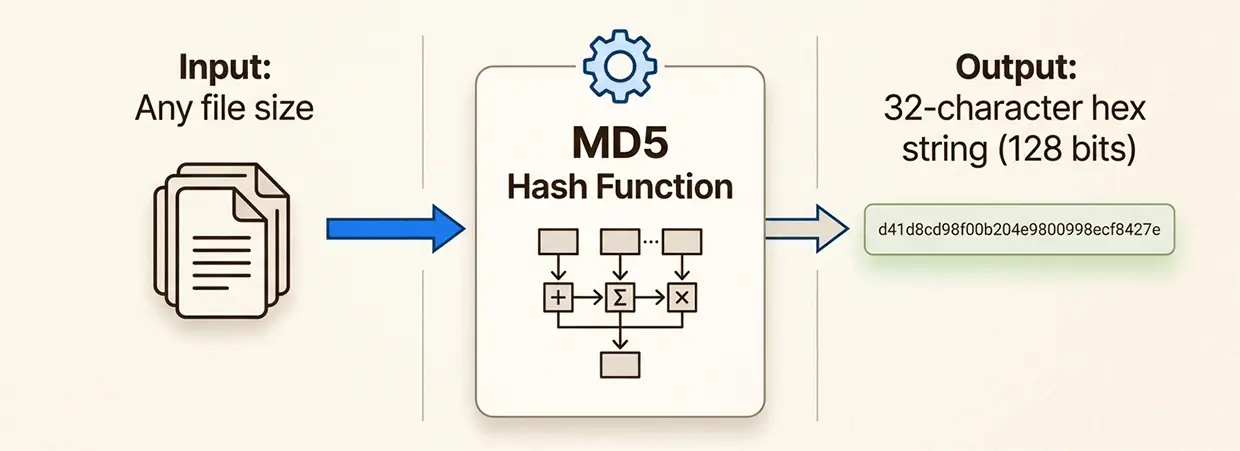
The core premise of any hash function is that even the smallest change to the input should produce a dramatically different output. Change a single bit in a file, and the MD5 hash changes completely. This property, known as the avalanche effect, makes hash functions valuable for verifying data integrity.
A collision occurs when two different inputs produce the same hash output. Mathematically, collisions must exist because there are infinitely many possible inputs but only a finite number of possible hash values (2^128, or approximately 3.4 × 10^38). This is the pigeonhole principle in action. If you have more pigeons than holes, some holes must contain multiple pigeons.
However, here is the critical distinction that many attorneys (and even some experts) miss. There are three distinct types of attacks against hash functions:
- Collision attacks involve finding any two inputs that produce the same hash. The attacker controls both inputs and can craft them specifically to collide. This is what researchers demonstrated against MD5 starting in 2004.
- Preimage attacks involve taking an existing hash value and finding an input that produces it. The attacker does not control the target hash. They must find a specific input that matches a predetermined output.
- Second preimage attacks involve taking a specific input and finding a different input that produces the same hash. This is more difficult than a collision attack because one of the inputs is already fixed.
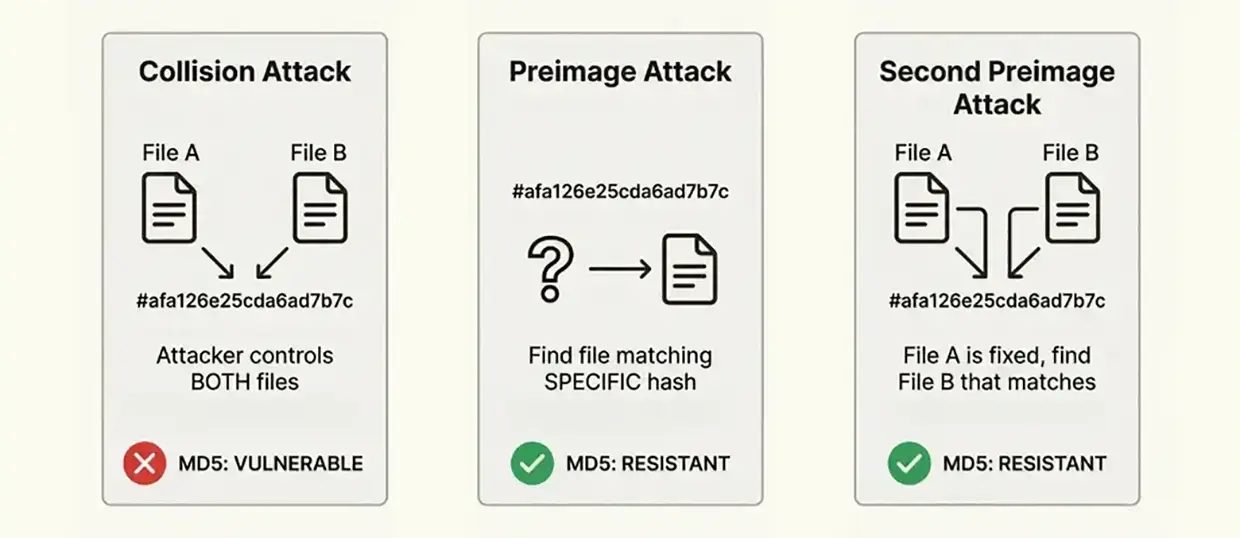
MD5 is broken against collision attacks. Since 2004, when Xiaoyun Wang and her colleagues announced the first practical collision attack, researchers have continuously improved collision generation techniques. Today, using freely available tools like fastcoll, a technically proficient person can generate MD5 collisions on a standard laptop in seconds.
But MD5 remains secure against preimage attacks. No one has demonstrated a feasible method to generate a file that matches a specific, predetermined MD5 hash. The computational requirements remain astronomically high, making such attacks theoretically possible but practically impossible with current technology.
For forensic purposes, this distinction is everything. When we verify evidence integrity, we are checking whether a file matches its expected hash. We are not asking whether someone could create two files that happen to collide. We are asking whether someone could tamper with our evidence and produce a file that matches the hash we already recorded. That is a preimage attack, not a collision attack.
Why MD5 Hash Integrity Matters in Digital Forensics
Digital evidence presents unique challenges for the legal system. Unlike physical evidence, digital data can be altered without leaving obvious traces. A single bit flipped in a document can change its meaning entirely while leaving the file size and modification date unchanged.
Hash functions provide the solution to this problem. According to the Scientific Working Group on Digital Evidence (SWGDE), "Digital Evidence submitted for examination should be maintained in such a way that the integrity of the data is preserved. The commonly accepted method to achieve this is to use a hashing function."
The forensic workflow relies on hash verification at multiple stages:
- Acquisition: When creating a forensic image of a drive, the examiner calculates and records the MD5 hash of the original evidence.
- Verification: After acquisition, the examiner verifies that the image hash matches the original, confirming an exact bit-for-bit copy.
- Analysis: Throughout examination, working copies are periodically verified against the known-good hash.
- Disclosure: When providing evidence to opposing parties, the hash ensures the received copy matches what was produced.
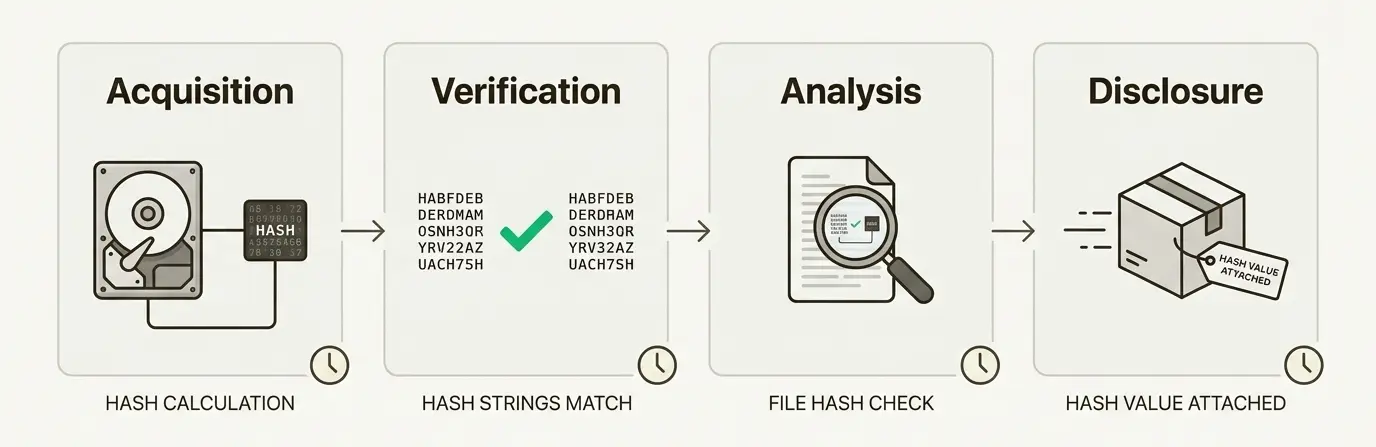
Under the Daubert standard, forensic methodologies must be reliable and generally accepted in the relevant scientific community. Hash verification meets this standard. It is objective, repeatable, and based on well-established mathematical principles. Courts have consistently admitted hash-verified evidence, provided the methodology is properly documented and explained.
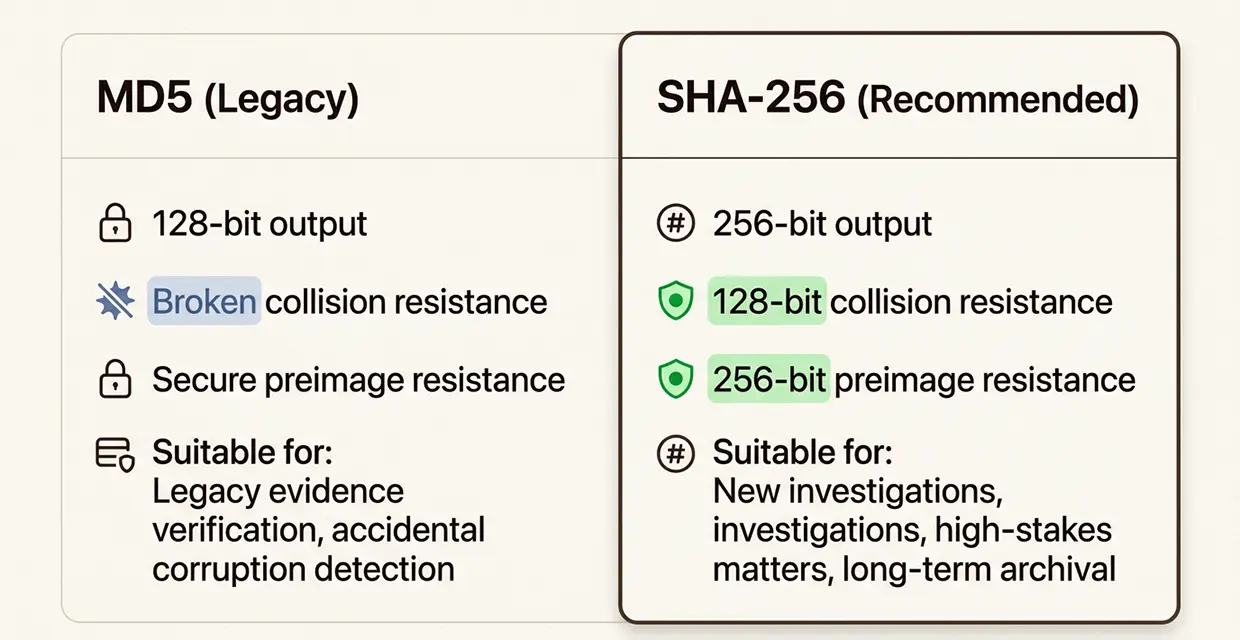
NIST, while deprecating MD5 for new cryptographic applications, has not invalidated its use for integrity verification. The National Institute of Standards and Technology specifies SHA-256 and other SHA-2 family algorithms as currently approved for generating message digests. However, the cryptographic properties that make MD5 unsuitable for new security applications (broken collision resistance) do not invalidate its utility for detecting accidental corruption or demonstrating chain of custody.
Common Misconceptions About MD5 Collisions (What Opposing Counsel Gets Wrong)
When MD5 vulnerabilities are raised in court, they are often accompanied by misconceptions that conflate different types of cryptographic attacks. Here are the most common errors we encounter when defending hash-based evidence integrity.
Misconception 1: "MD5 is broken, so all MD5-hashed evidence is compromised."
This overbroad statement conflates collision vulnerability with preimage vulnerability. While MD5 is cryptographically broken for collision resistance, it remains secure against preimage attacks. Creating a useful collision requires specific conditions: the attacker must control the content of both colliding files, and the collision must be engineered before the hash is recorded. No one has demonstrated a method to retroactively tamper with evidence and produce a matching hash. For integrity verification against accidental corruption or demonstrating chain of custody, MD5 remains functionally sound.
Misconception 2: "Hash collisions happen randomly in the wild."
This claim has no basis in documented reality. No accidental or naturally occurring MD5 collision has been observed to date in real-world data. The probability of a random collision is approximately 1.47 × 10^-29, making it astronomically unlikely. To put this in perspective, you are more likely to win the Powerball lottery while being struck by lightning than to encounter an accidental MD5 collision in forensic data. All documented collisions have been deliberately engineered by researchers using specialized tools and techniques.
Misconception 3: "If collisions exist, someone could have swapped evidence files."
This argument fails to understand the mechanics of collision attacks. Creating a collision requires controlling the content of both files that will collide. An attacker cannot take an existing evidence file, modify it to contain incriminating/decriminating material, and then somehow make it match the original hash. The collision must be engineered into both files from the beginning. For evidence that was collected and hashed before any tampering opportunity existed, collision attacks are simply not applicable.
Misconception 4: "MD5 collisions are easy to generate, so attacks are trivial."
While collision generation tools like fastcoll are freely available, creating meaningful collisions requires significant technical sophistication. The colliding files produced by these tools contain carefully crafted binary data that differs in specific ways while maintaining the same hash. Creating two executable files with the same MD5 hash but different malicious behaviors, for example, requires expertise in both cryptography and file format manipulation. While this is within the capabilities of determined attackers, it is far from trivial.
Real-World MD5 Exploitation: The Flame Malware Case Study
To understand when MD5 collisions actually matter, we must examine the only confirmed real-world exploitation of MD5 collision vulnerabilities: the Flame malware incident of 2012.
Flame was sophisticated espionage malware that targeted systems in the Middle East. What made Flame remarkable from a cryptographic perspective was its use of a novel MD5 collision attack to forge Microsoft code-signing certificates.
Here is how the attack worked. Microsoft used MD5-based certificates for their Terminal Services Licensing infrastructure. These certificates chained up to the same root certificate authority that signed legitimate Windows Update packages. The attackers discovered that they could request a Terminal Services certificate with carefully crafted parameters, then use a chosen-prefix collision attack to create a parallel certificate with the code-signing bit enabled.
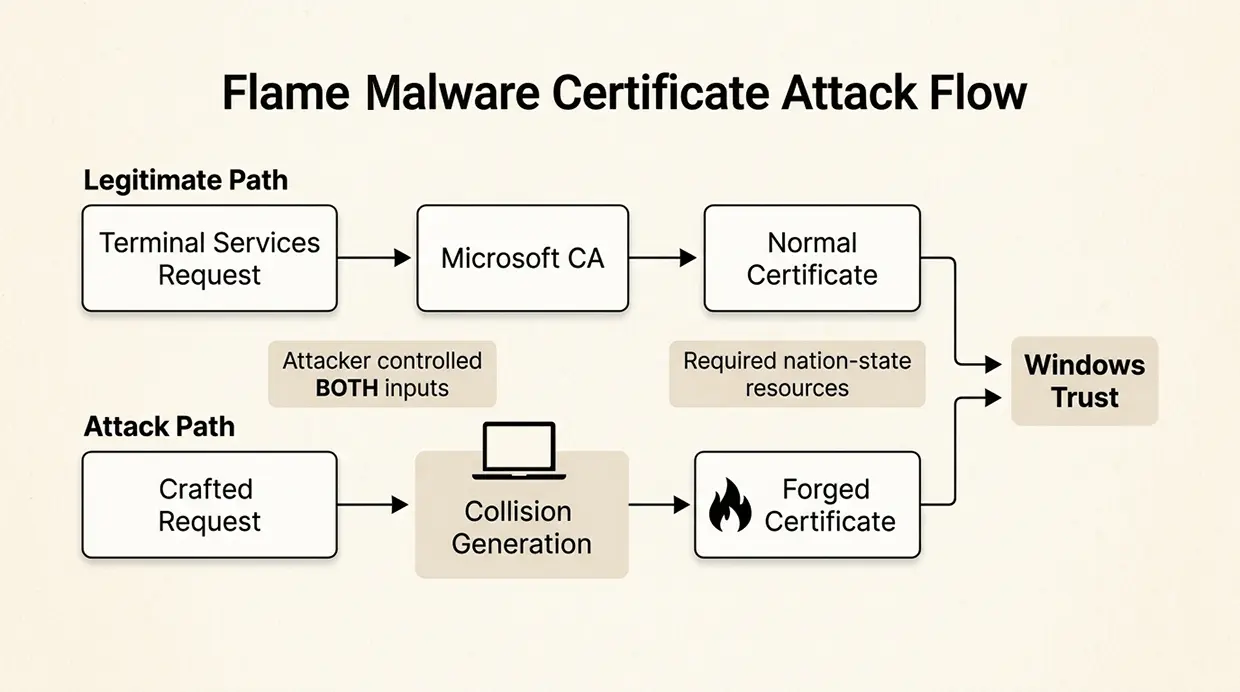
Marc Stevens, one of the world's leading MD5 collision researchers at CWI (Centrum Wiskunde and Informatica), analyzed the Flame collision and confirmed it used "a completely new variant of a chosen prefix collision attack." His assessment: "The design of this new variant required world-class cryptanalysis."
This case reveals several critical facts about real-world MD5 exploitation:
First, the attack required nation-state-level resources. The collision technique was novel, suggesting significant investment in cryptographic research.
Second, the attack required advance planning. The attackers had to understand Microsoft's certificate infrastructure, identify the vulnerability, and engineer the collision before obtaining the certificate.
Third, the attack targeted a specific cryptographic application (code signing) where collision attacks are relevant. The attackers controlled the certificate request and could craft it to enable collision generation.
For forensic evidence integrity, the Flame case actually supports the defense of MD5 rather than undermining it. The attack demonstrates that collision exploitation requires specific conditions that do not exist in standard forensic workflows. An examiner who hashes evidence at acquisition controls the timing and context of the hash. There is not an opportunity for an attacker to engineer a collision after the fact.
Legal and Courtroom Implications: Defending MD5 Evidence Under Challenge
When opposing counsel raises MD5 collision concerns, a prepared expert can address these challenges methodically and effectively. Here is how we approach these questions in our testimony.
Establish the specific attack scenario. Begin by asking what specific attack the defense is alleging. Are they claiming that the evidence was intentionally manipulated using collision attacks? If so, what evidence supports this claim? The defense bears the burden of establishing a plausible attack vector with supporting facts, not just raising theoretical cryptographic concerns.
Distinguish collision resistance from preimage resistance. Explain clearly that MD5's broken collision resistance does not imply broken preimage resistance. Use accessible language: "Creating two files that happen to have the same fingerprint is very different from creating a file that matches a fingerprint I already have in my notes. MD5 remains secure against the second scenario."
Address the wild versus engineered distinction. Emphasize that all documented MD5 collisions result from deliberate engineering using specialized tools. No naturally occurring collision has ever been observed. The statistical probability is so low that accidental collisions can be ruled out as a practical matter.
Contextualize within the forensic workflow. Explain how hash verification fits into the broader chain of custody. Hash values are recorded in contemporaneous notes, verified at multiple stages, and often supplemented by other integrity indicators like file system timestamps and forensic software logs. A sophisticated attack would need to compromise all of these verification mechanisms simultaneously.
Acknowledge when MD5 challenges may have merit. Intellectual honesty strengthens credibility. If evidence originates from an untrusted source with both motive and technical capability, or if there are suspicious circumstances like files with identical MD5 hashes but visibly different content, these warrant investigation. In such cases, upgrading to SHA-256 verification or seeking additional corroborating evidence may be appropriate.
The key is to neither dismiss MD5 vulnerabilities nor exaggerate their relevance to forensic integrity verification. Accurate, nuanced testimony serves the court and strengthens the expert's credibility.
Best Practices for Forensic Examiners: When to Use MD5 vs. Modern Alternatives
At Black Dog Forensics, we follow current NIST and industry guidance while recognizing the practical realities of legacy evidence and existing workflows.
For new investigations: We use SHA-256 and MD5 as our primary hash algorithms. NIST's Computer Security Resource Center specifies SHA-256 as an approved hash algorithm under FIPS 180-4. The SHA-2 family provides 128 bits of collision resistance and 256 bits of preimage resistance, significantly exceeding MD5's security levels even before MD5's collision vulnerabilities were discovered.
We also generate MD5 hashes concurrently for backward compatibility. Many forensic tools and opposing experts still expect MD5 values, and providing both algorithms ensures compatibility while prioritizing security.
For expert reports: We specify which hash algorithms were used for evidence verification and include a brief explanation of their purpose. Addressing hash methodology proactively in reports often prevents challenges during testimony.
Following SWGDE guidance, we document our procedures thoroughly. "It is incumbent upon the examiner to document all procedures used," and we take this responsibility seriously.
Key Takeaways for Attorneys and Forensic Examiners
- MD5 collisions are real but require deliberate engineering. They do not occur naturally in the wild.
- No documented case exists of accidental MD5 collision in real-world files.
- Preimage attacks against MD5 remain computationally infeasible. No one can generate a file that matches a specific, predetermined MD5 hash that wasn't engineered.
- MD5 remains adequate for verifying evidence integrity against accidental corruption and demonstrating chain of custody.
- Best practice for new matters is to use SHA-256 while maintaining MD5 for backward compatibility.
- Opposing counsel's MD5 challenge requires a specific attack allegation with supporting evidence, not just vague cryptographic fear.
- Expert testimony should clearly distinguish collision attacks from preimage attacks to help the court understand the actual risks.
Trust Black Dog Forensics for Defensible Digital Evidence Analysis
At Black Dog Forensics, we understand that digital evidence must meet the highest standards of technical rigor and legal admissibility. Our examiners stay current with NIST guidance, SWGDE best practices, and evolving cryptographic research. We document our methodologies thoroughly and present our findings with the clarity and precision that courts demand.
Whether you need forensic imaging, evidence analysis, or expert testimony, we deliver results that withstand scrutiny. Like a loyal retriever, we dig deep and follow the digital trail with focus and integrity. Our mission is simple: retrieve the truth.
Contact Black Dog Forensics today to discuss your digital evidence needs. We serve clients nationwide from our offices in Texas and Colorado, and our expertise has been recognized by media outlets including Dateline NBC.




 346-200-6097
346-200-6097



